Cs-Cr
Crippling Crypto-Ransomware

Differential Privacy: on the trade-off between Utility and Information Leakage

Do Smarter People Have Better Passwords?
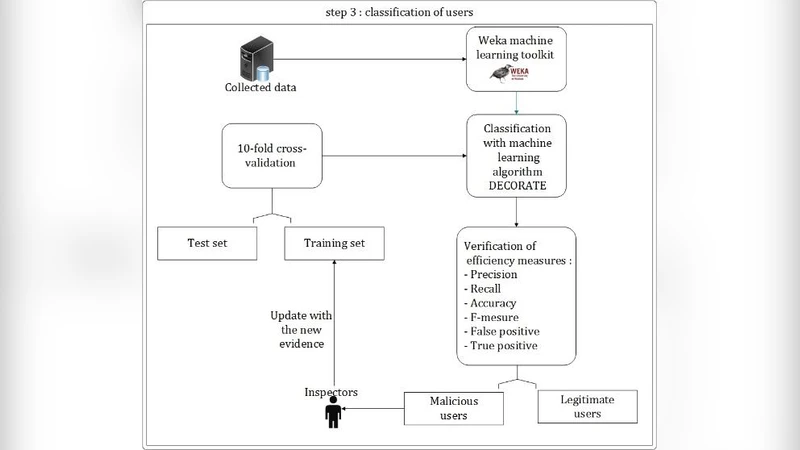
A security approach based on honeypots: Protecting Online Social network from malicious profiles
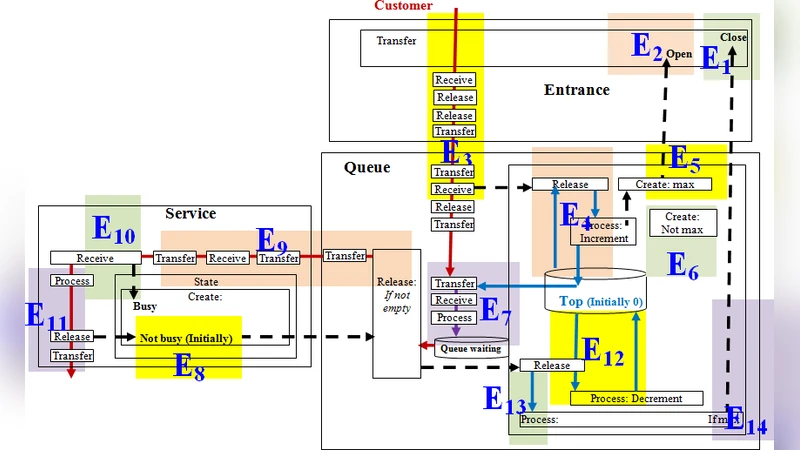
Authentication Modeling with Five Generic Processes
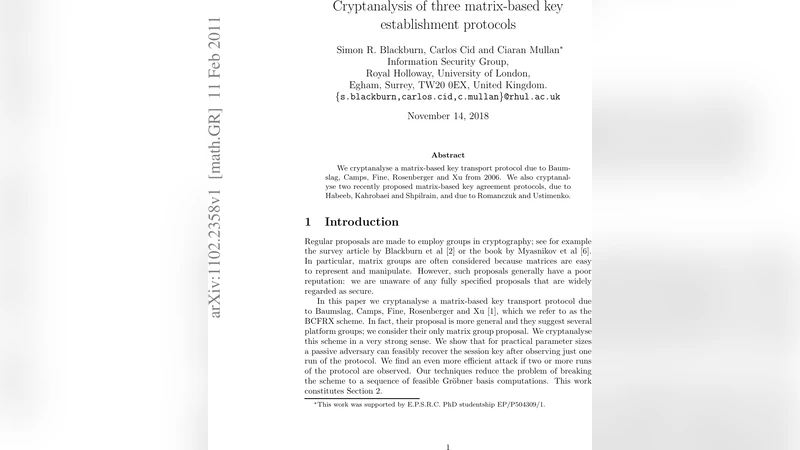
Cryptanalysis of three matrix-based key establishment protocols
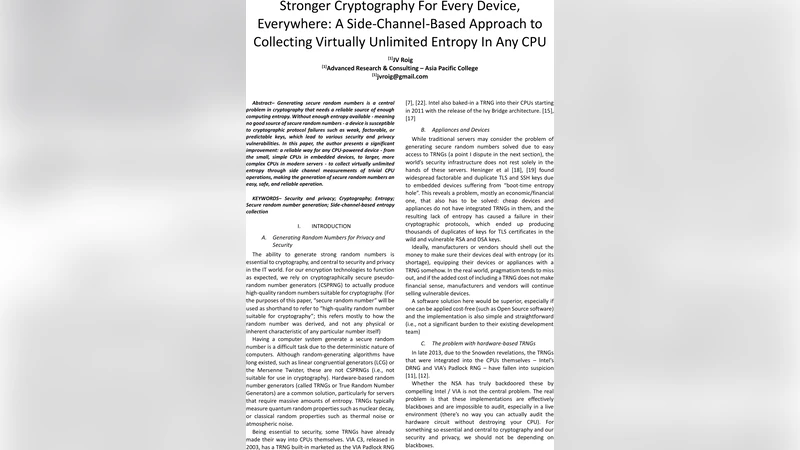
Stronger Cryptography For Every Device, Everywhere

Why developers cannot embed privacy into software systems? An empirical investigation

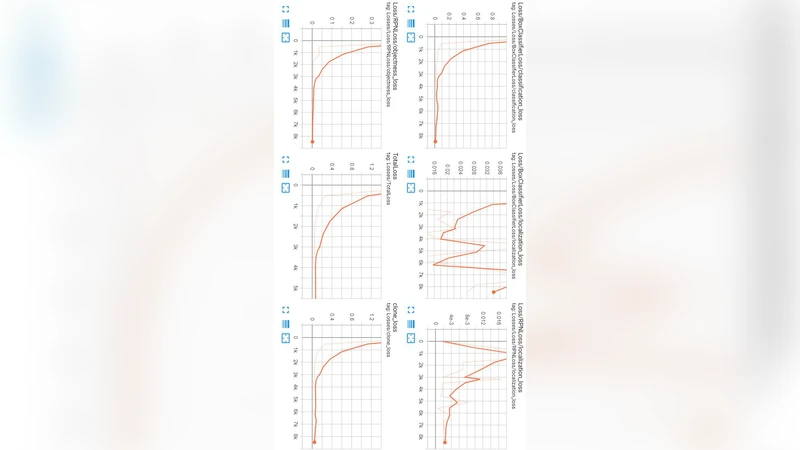
Towards Practical Privacy-Preserving Analytics for IoT and Cloud Based Healthcare Systems

State Space Reduction in the Maude-NRL Protocol Analyzer
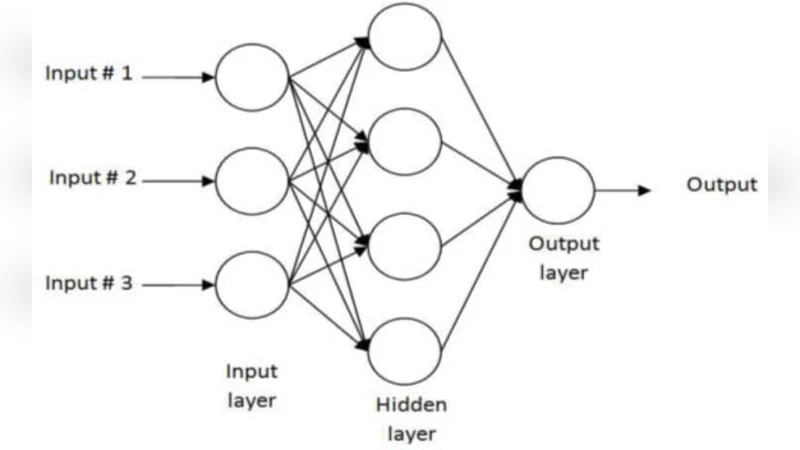
Machine Learning Methods for Network Intrusion Detection
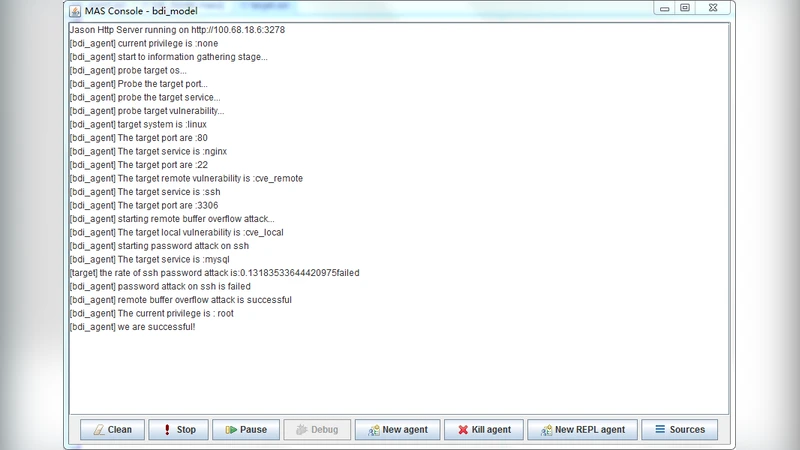
Agent-based (BDI) modeling for automation of penetration testing

Detecting Anomalous Process Behaviour using Second Generation Artificial Immune Systems

Using Repeating Decimals As An Alternative To Prime Numbers In Encryption
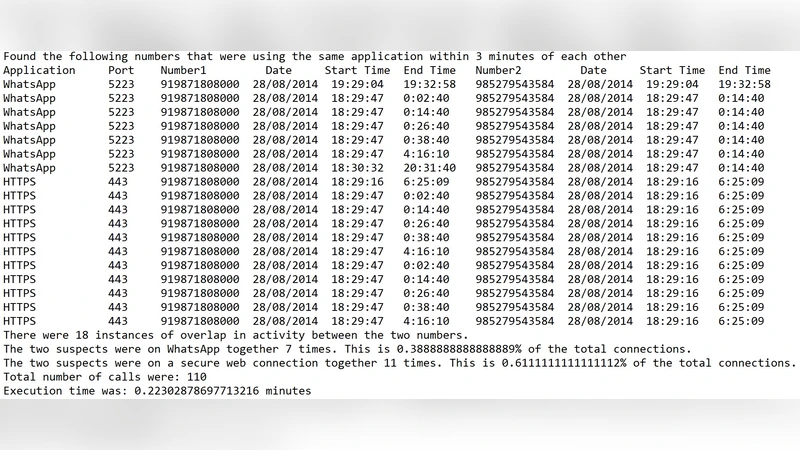
Analyzing CDR/IPDR data to find People Network from Encrypted Messaging Services
AI-Powered GUI Attack and Its Defensive Methods
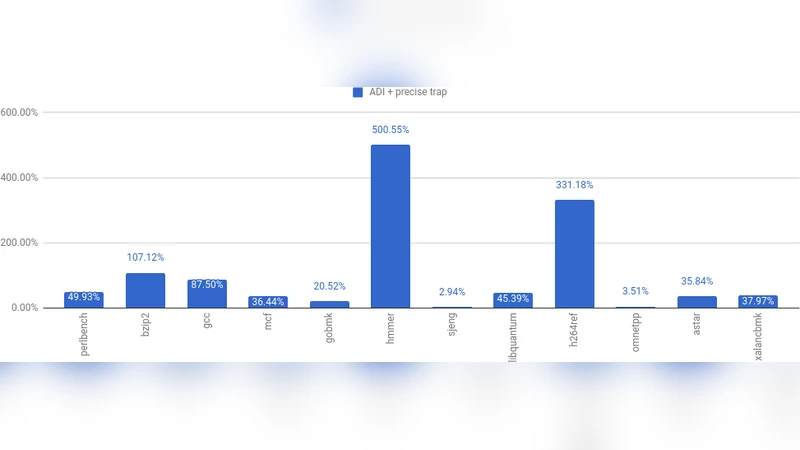
Memory Tagging and how it improves C/C++ memory safety

Stronger Enforcement of Security Using AOP and Spring AOP
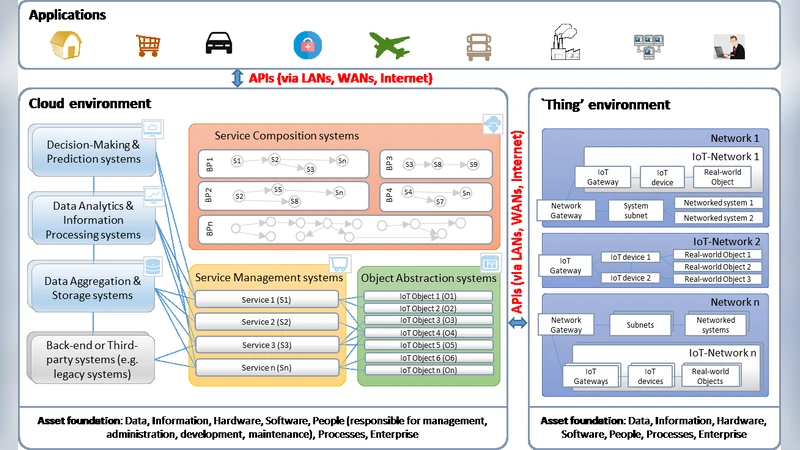
Security Risk Assessment in Internet of Things Systems
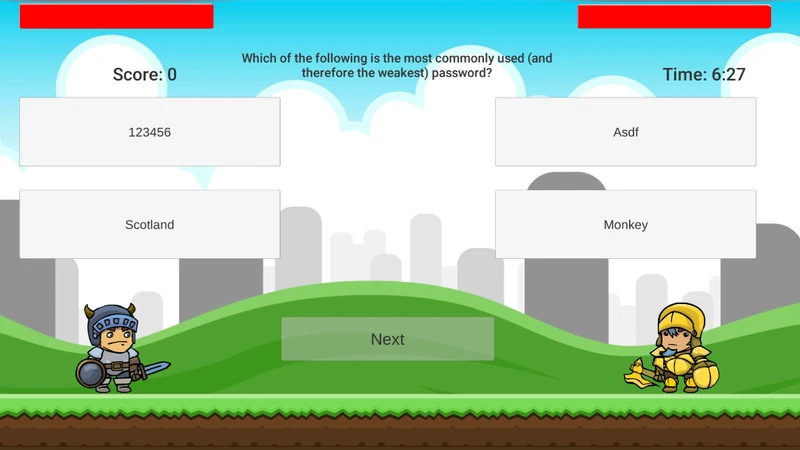
Gamification Techniques for Raising Cyber Security Awareness
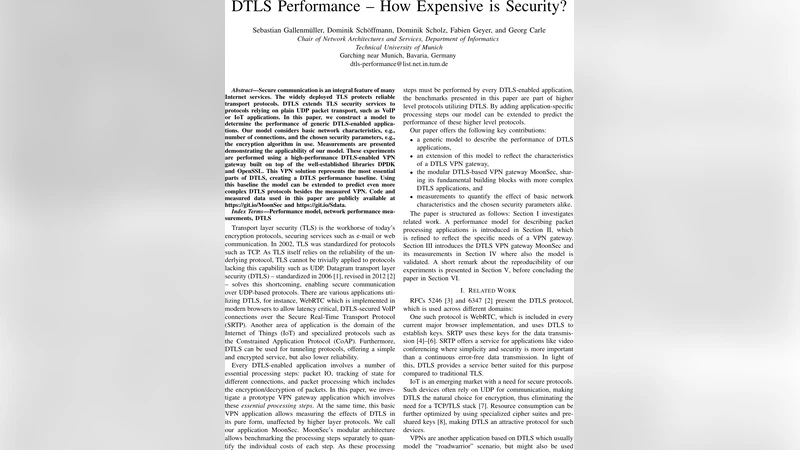
DTLS Performance - How Expensive is Security?
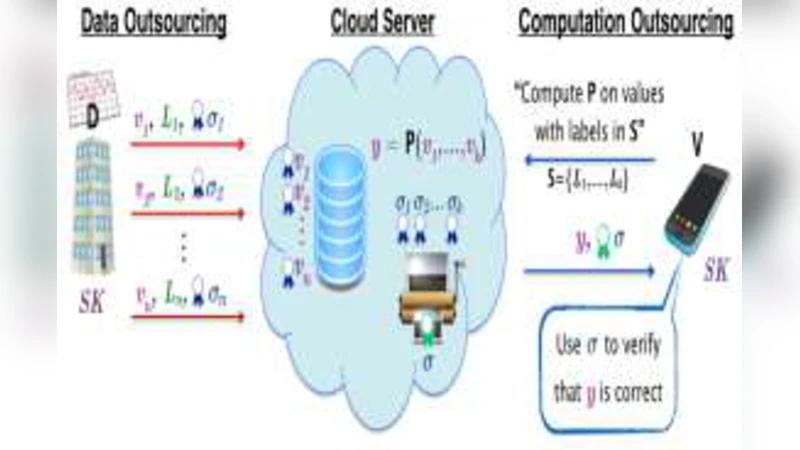
A Verifiable Fully Homomorphic Encryption Scheme for Cloud Computing Security