Cs-Cr

Secure Satellite Communication Systems Design with Individual Secrecy Rate Constraints

Secure Neighbor Position Discovery in VANETs

Security Features of an Asymmetric Cryptosystem based on the Diophantine Equation Hard Problem

DNA based Network Model and Blockchain

Fail-Stop Group Signature Scheme

Considerations regarding security issues impact on systems availability
Why Johnny Cant Store Passwords Securely? A Usability Evaluation of Bouncycastle Password Hashing

A Fast Combination of AES Encryption and LZ4 Compression Algorithms

Malware static analysis and DDoS capabilities detection

A methodology to Evaluate the Usability of Security APIs

Applications of Blockchain Technology beyond Cryptocurrency
Adapting Blockchain Technology for Scientific Computing
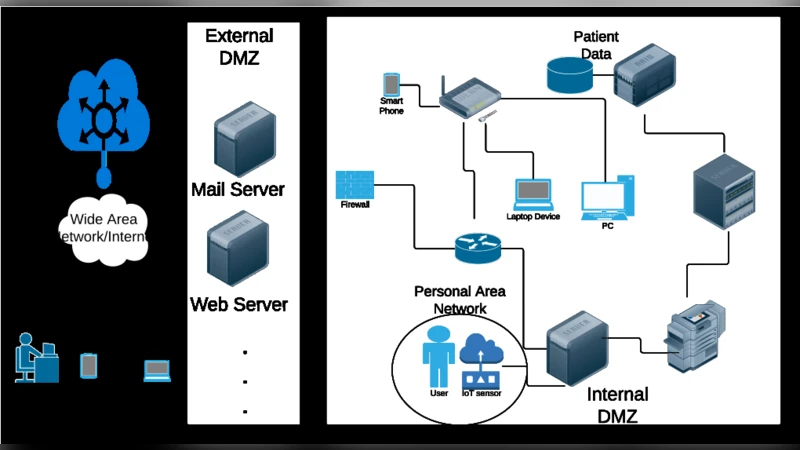
BYOD, Personal Area Networks (PANs) and IOT: Threats to Patients Privacy

An In-depth Analysis of Spam and Spammers
Exchanging Secrets without Using Cryptography
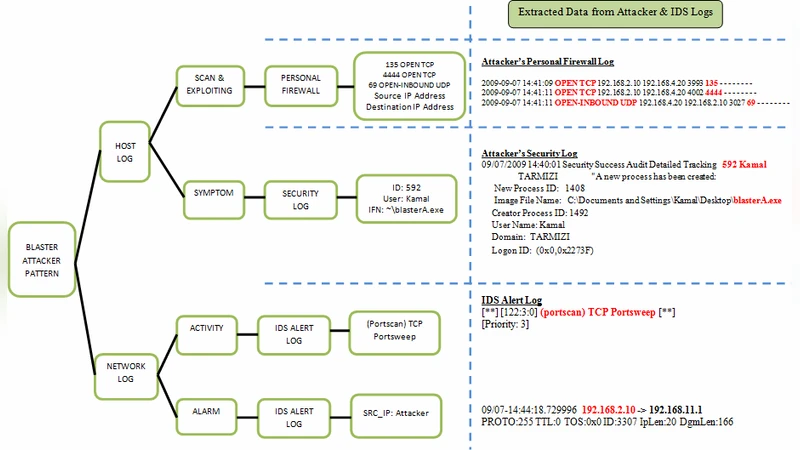
New Multi-step Worm Attack Model

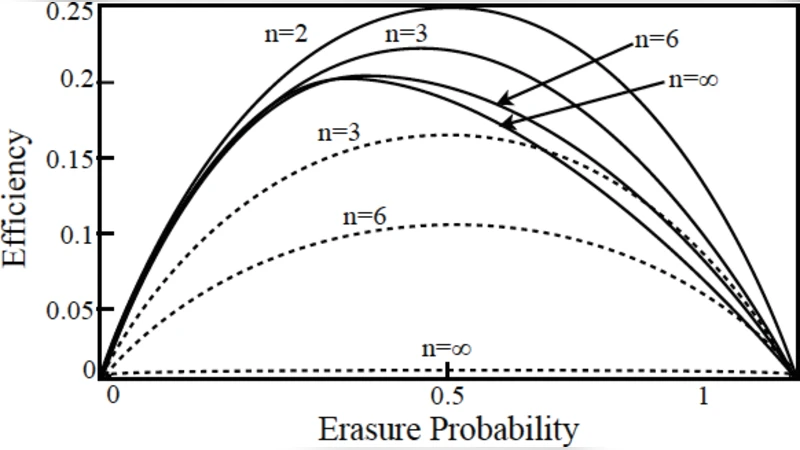
Selecting efficient and reliable preservation strategies: modeling long-term information integrity using large-scale hierarchical discrete event simulation
Sparse Random Approximation and Lossy Compression

Breaking an image encryption scheme based on Arnold map and Lucas series

The Secure Machine: Efficient Secure Execution On Untrusted Platforms

Synthesis of Parallel Binary Machines

LinBFT: Linear-Communication Byzantine Fault Tolerance for Public Blockchains
