Cs-Cr
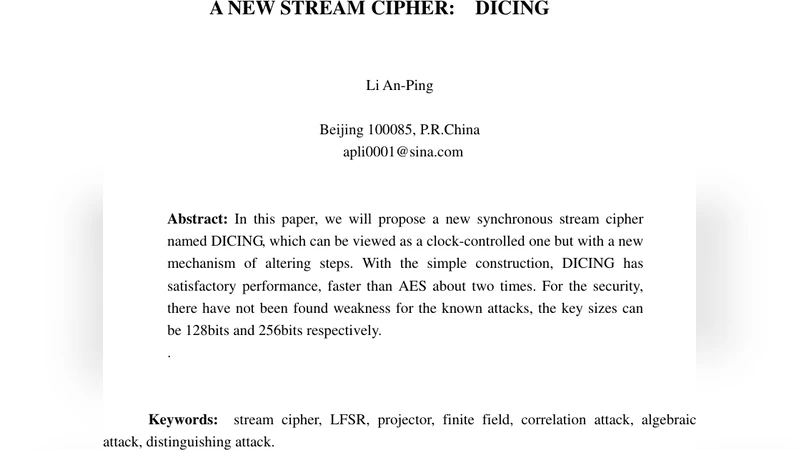
Closed-Form Expressions for Secrecy Capacity over Correlated Rayleigh Fading Channels

Execution Models for Choreographies and Cryptoprotocols

Factoring with Hints

Quantum Fourier sampling, Code Equivalence, and the quantum security of the McEliece and Sidelnikov cryptosystems

Security of a biometric identity-based encryption scheme
WiFi Epidemiology: Can Your Neighbors Router Make Yours Sick?
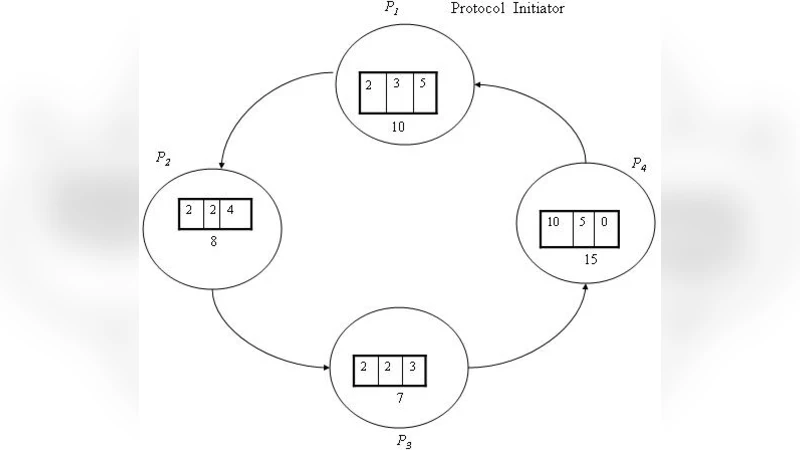
Changing Neighbors k Secure Sum Protocol for Secure Multi Party Computation
Java Components Vulnerabilities - An Experimental Classification Targeted at the OSGi Platform

Deciding security properties for cryptographic protocols. Application to key cycles
Cryptography in the Bounded-Quantum-Storage Model
Space Efficient Secret Sharing
KRNC: New Foundations for Permissionless Byzantine Consensus and Global Monetary Stability
Oblivious Transfer based on Key Exchange
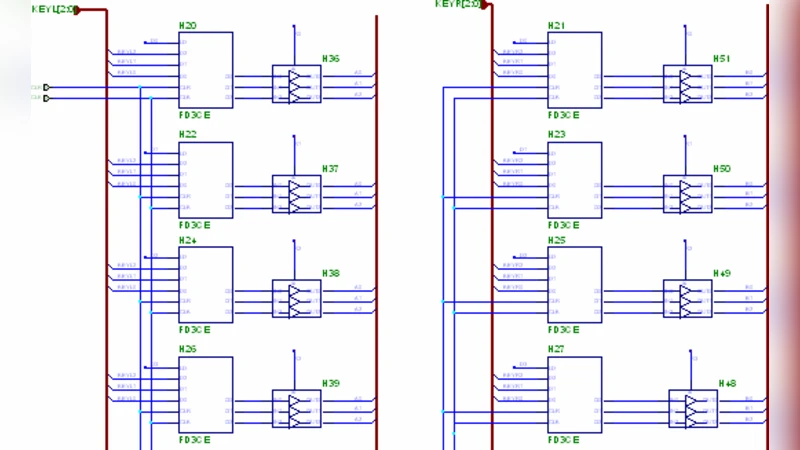
An Improved FPGA Implementation of the Modified Hybrid Hiding Encryption Algorithm (MHHEA) for Data Communication Security

Automatic Methods for Analyzing Non-Repudiation Protocols with an Active Intruder

A New Key-Agreement-Protocol
Achievable Rates for Two-Way Wire-Tap Channels
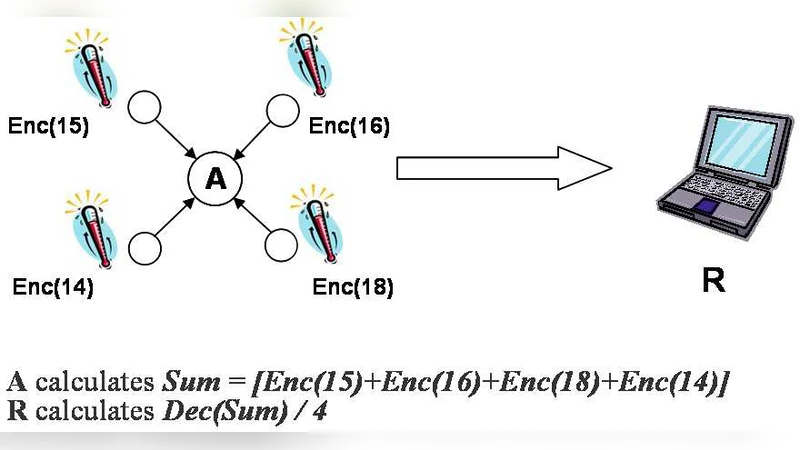
Optimized Implementation of Elliptic Curve Based Additive Homomorphic Encryption for Wireless Sensor Networks
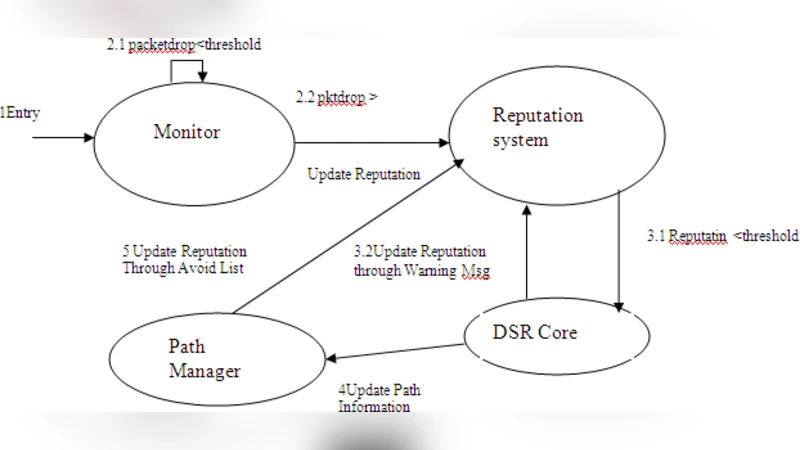
A Novel Method for Intrusion Detection System to Enhance Security in Ad hoc Network
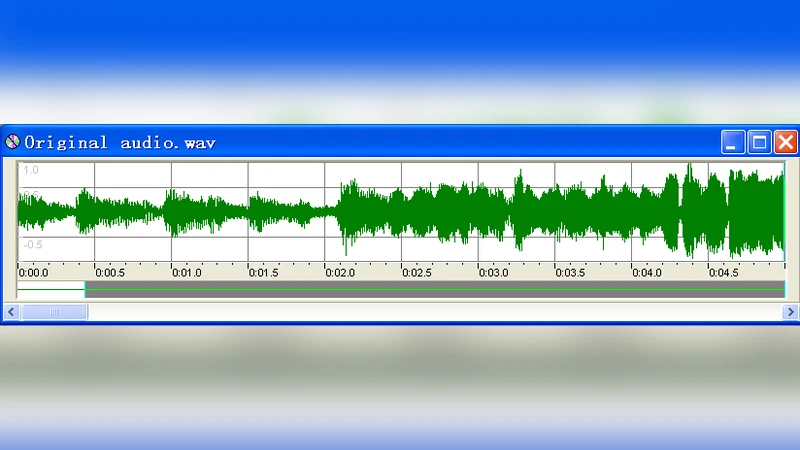
Robust Audio Watermarking Against the D/A and A/D conversions
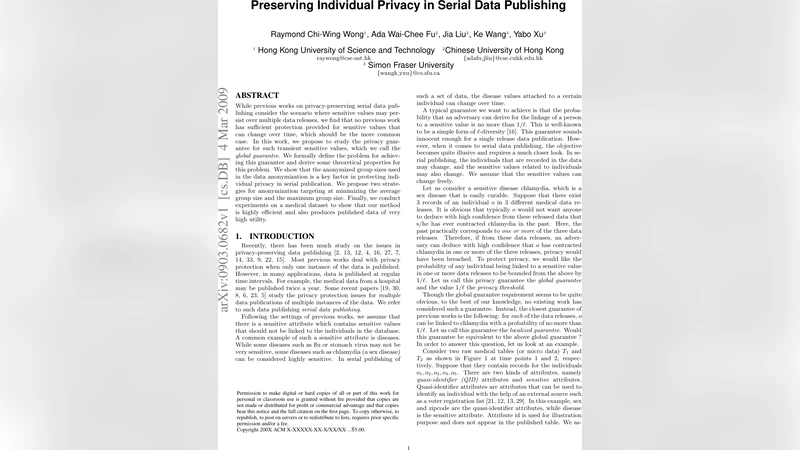
Preserving Individual Privacy in Serial Data Publishing
Security Estimates for Quadratic Field Based Cryptosystems
