Cs-Cr

An Efficient Encryption Algorithm for P2P Networks Robust Against Man-in-the-Middle Adversary
An Incomplete Cryptography based Digital Rights Management with DCFF

An ISP Level Solution to Combat DDoS Attacks using Combined Statistical Based Approach
Analysis of Intelligent Classifiers and Enhancing the Detection Accuracy for Intrusion Detection System

Analysis of RSA algorithm using GPU programming
Andlantis: Large-scale Android Dynamic Analysis
Authentication System for Smart Homes Based on ARM7TDMI-S and IRIS-Fingerprint Recognition Technologies
Because we care: Privacy Dashboard on Firefox OS

BitWhisper: Covert Signaling Channel between Air-Gapped Computers using Thermal Manipulations

Cloud-Aware Web Service Security: Information Hiding in Cloud Computing
Context, Content, Process Approach to Align Information Security Investments with Overall Organizational Strategy
Convergence Rates for Differentially Private Statistical Estimation
Countering Social Engineering through Social Media: An Enterprise Security Perspective

Cyber Security of Smart Grid Infrastructure
Danger is My Middle Name: Experimenting with SSL Vulnerabilities in Android Apps

Data Minimisation in Communication Protocols: A Formal Analysis Framework and Application to Identity Management
Defending Grey Attacks by Exploiting Wavelet Analysis in Collaborative Filtering Recommender Systems
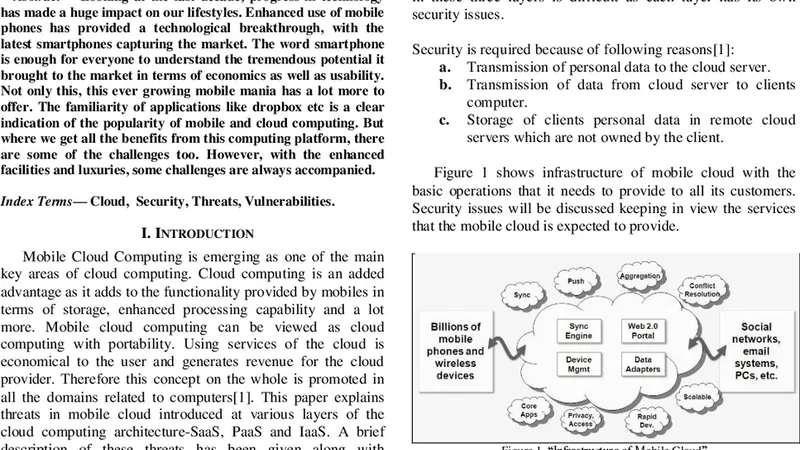
Delving into the Security Issues of Mobile Cloud Computing

Differentially Private Iterative Synchronous Consensus
Dynamic Traitor Tracing for Arbitrary Alphabets: Divide and Conquer

Eavesdropping in Semiquantum Key Distribution Protocol
Embedding grayscale halftone pictures in QR Codes using Correction Trees