Cs-Cr

On the security of an enhanced short signature scheme

On the Use of Latency Graphs for the Construction of Tor Circuits
On-the fly AES Decryption/Encryption for Cloud SQL Databases
Optimized Password Recovery for Encrypted RAR on GPUs
Parameter security characterization of knapsack public-key crypto under quantum computing
Phishing Detection in IMs using Domain Ontology and CBA - An innovative Rule Generation Approach
Practical Solutions For Format-Preserving Encryption
Preventing SQL Injection attack using pattern matching algorithm
Recovering Residual Forensic Data from Smartphone Interactions with Cloud Storage Providers
Reed-Muller Realization of X (mod P)
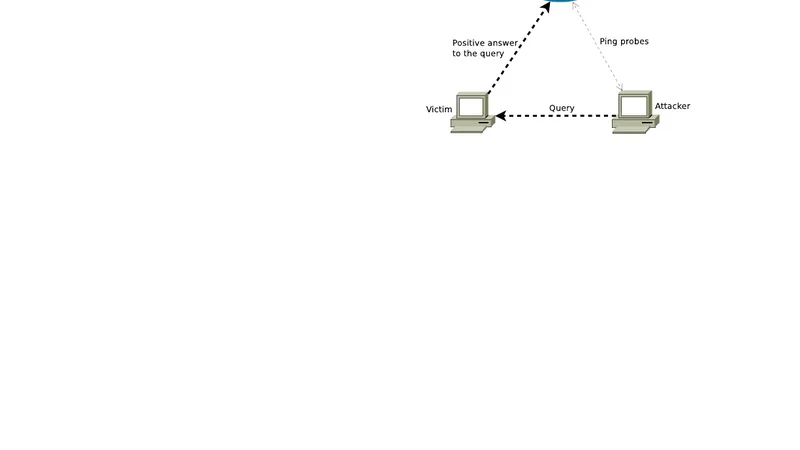
Reflection Scan: an Off-Path Attack on TCP

RFID Security Using Lightweight Mutual Authentication And Ownership Transfer Protocol

Scaling efficient code-based cryptosystems for embedded platforms
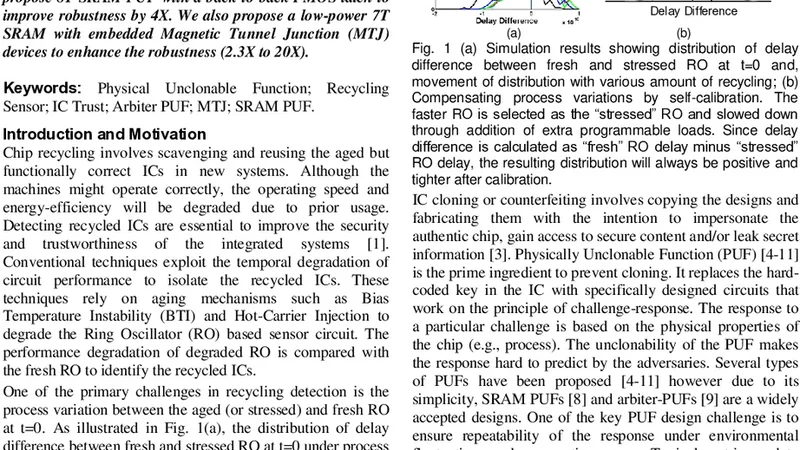
Schmitt-Trigger-based Recycling Sensor and Robust and High-Quality PUFs for Counterfeit IC Detection
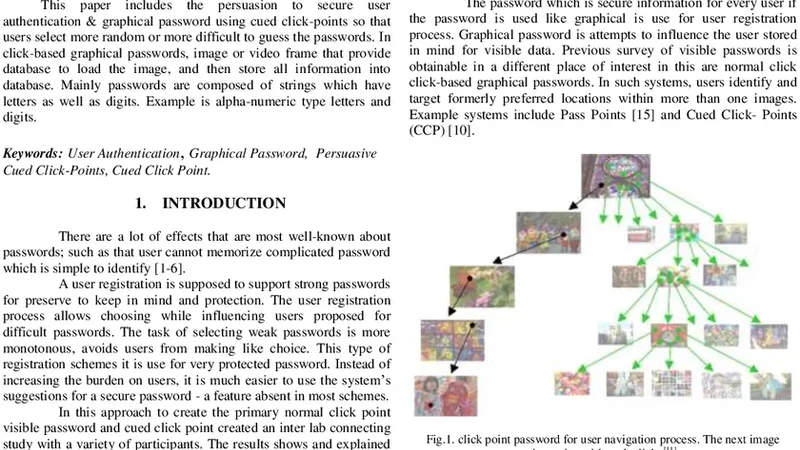
Secure User Authentication & Graphical Password using Cued Click-Points
Security challenges in mobile ad hoc networks:a survey

Security Incident Response Criteria: A Practitioners Perspective
Security Risks in Mechanical Engineering Industries
Semi-autonomous, context-aware, agent using behaviour modelling and reputation systems to authorize data operation in the Internet of Things
Simulation of Collision Resistant Secure Sum Protocol
SODEXO: A System Framework for Deployment and Exploitation of Deceptive Honeybots in Social Networks
StegBlocks: ensuring perfect undetectability of network steganography