Cs-Cr
Analysis of Maximum Likelihood and Mahalanobis Distance for Identifying Cheating Anchor Nodes
Analyzing Cryptographic Algorithms for Secure Cloud Network
AODVSEC: A Novel Approach to Secure Ad Hoc on-Demand Distance Vector (AODV) Routing Protocol from Insider Attacks in MANETs
Applicability of DUKPT Key Management Scheme to Cloud Wallet and other Mobile Payments
Application of Multi factor authentication in Internet of Things domain
Applying recent secure element relay attack scenarios to the real world: Google Wallet Relay Attack

ASIA: An Access Control, Session Invocation and Authorization Architecture for Home Energy Appliances in Smart Energy Grid Environments
Assessing Inconspicuous Smartphone Authentication for Blind People
Attacks on quantum key distribution protocols that employ non-ITS authentication
Automated Verification Of Role-Based Access Control Policies Constraints Using Prover9

Chip and Skim: cloning EMV cards with the pre-play attack
Classification of Attacks in Wireless Sensor Networks
CloRoFor: Cloud Robust Forensics

Collaborative Applications over Peer-to-Peer Systems - Challenges and Solutions
Comparative Analysis of Cryptography Library in IoT
Complete Network Security Protection for SMEs within Limited Resources
Cryptography from Quantum mechanical viewpoint
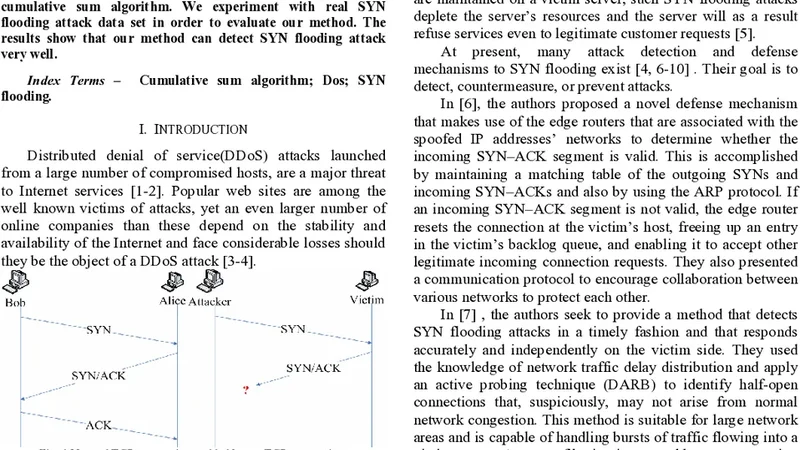
Cumulative Sum Algorithm for Detecting SYN Flooding Attacks
Data Migration among Different Clouds

Data Protection: Combining Fragmentation, Encryption, and Dispersion, a final report
Defeating the Kalka--Teicher--Tsaban linear algebra attack on the Algebraic Eraser

Defending against malicious peripherals with Cinch