Cs-Cr

Reversing the asymmetry in data exfiltration
Mathematical Modeling of Routes Maintenance and Recovery Procedure for MANETs

PIDS - A Behavioral Framework for Analysis and Detection of Network Printer Attacks
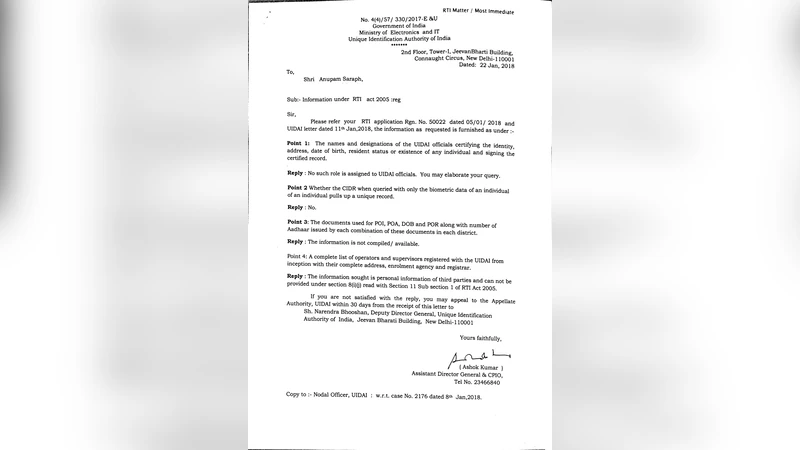
Is Indias Unique Identification Number a legally valid identification?

Camouflaged with Size: A Case Study of Espionage using Acquirable Single-Board Computers
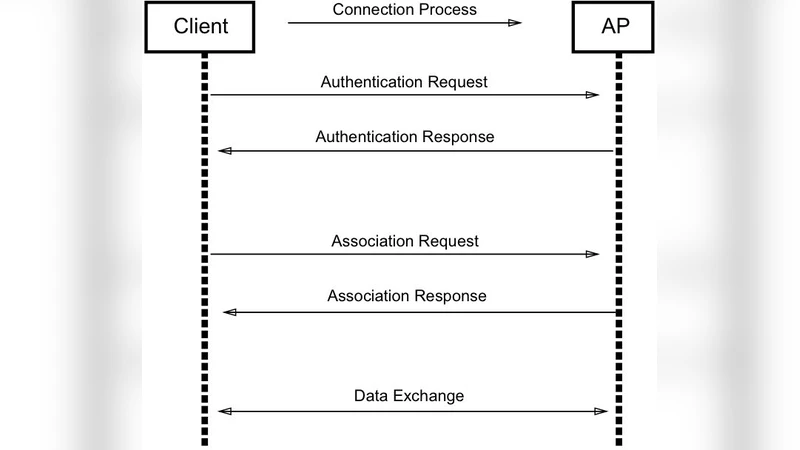
Preventing wireless deauthentication attacks over 802.11 Networks
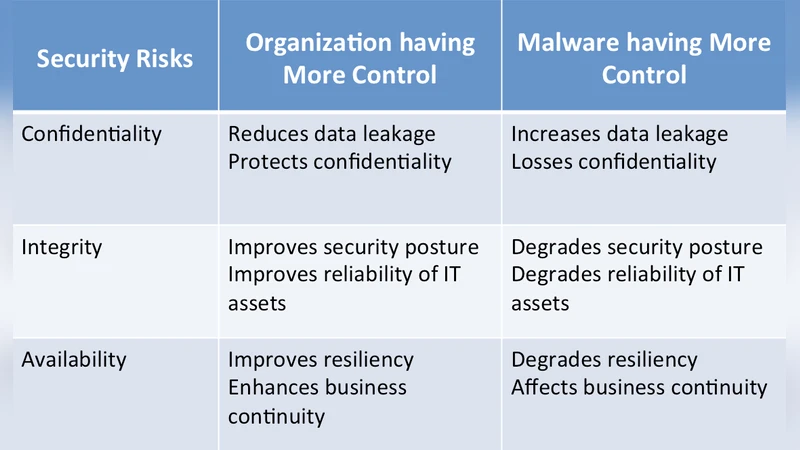
Using Malware Self-Defence Mechanism to Harden Defence and Remediation Tools

Isolated and Ensemble Audio Preprocessing Methods for Detecting Adversarial Examples against Automatic Speech Recognition

Building Confidence not to be Phished through a Gamified Approach: Conceptualising Users Self-Efficacy in Phishing Threat Avoidance Behaviour

Metamorphic Malware Detection Using Linear Discriminant Analysis and Graph Similarity

Security, Privacy and Safety Risk Assessment for Virtual Reality Learning Environment Applications
Synchronized Detection and Recovery of Steganographic Messages with Adversarial Learning

An Adaptable Maturity Strategy for Information Security

A Robust Mechanism for Defending Distributed Denial OF Service Attacks on Web Servers

Generative Steganography by Sampling
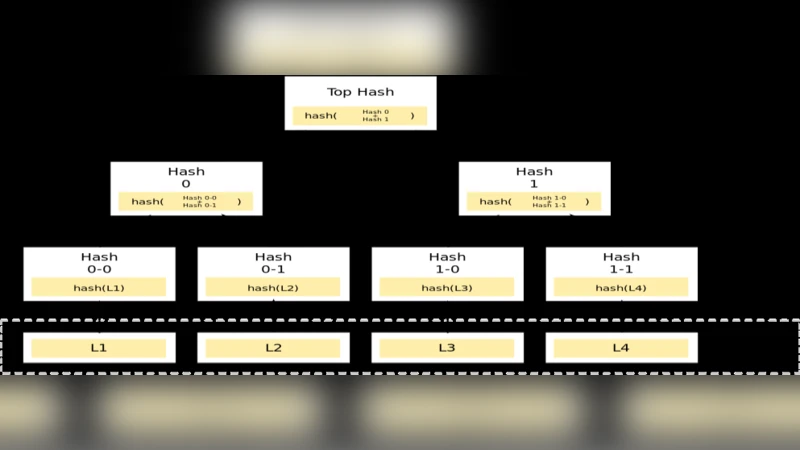
A survey of blockchain frameworks and applications

Design of a New Stream Cipher: PALS
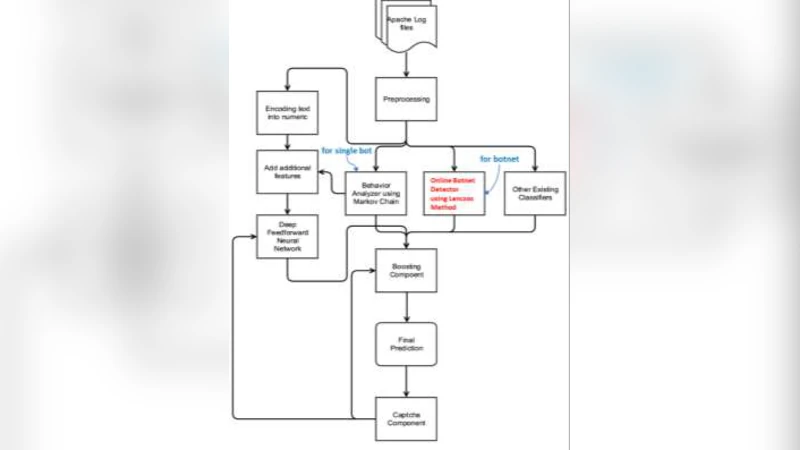
Fast Botnet Detection From Streaming Logs Using Online Lanczos Method
Data Security and Privacy Protection Data Security and Privacy Protection in Public Cloud
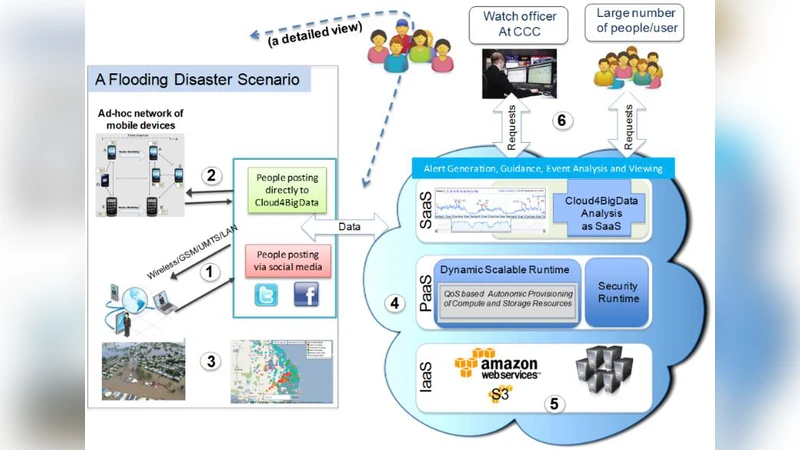
Internet of Things (IoT) and Cloud Computing Enabled Disaster Management
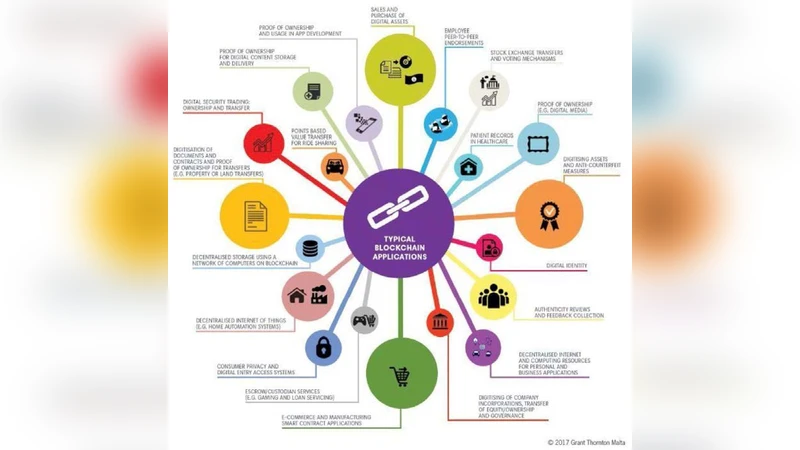
Blockchain Enabled Enhanced IoT Ecosystem Security
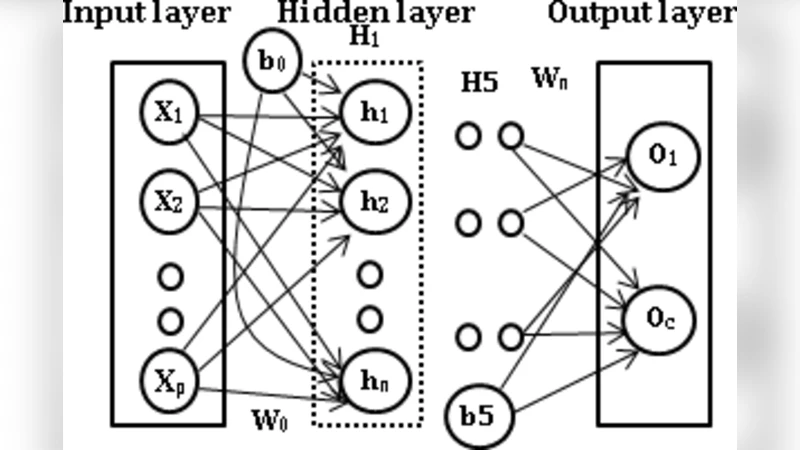
Deep-Net: Deep Neural Network for Cyber Security Use Cases