Cs-Cr

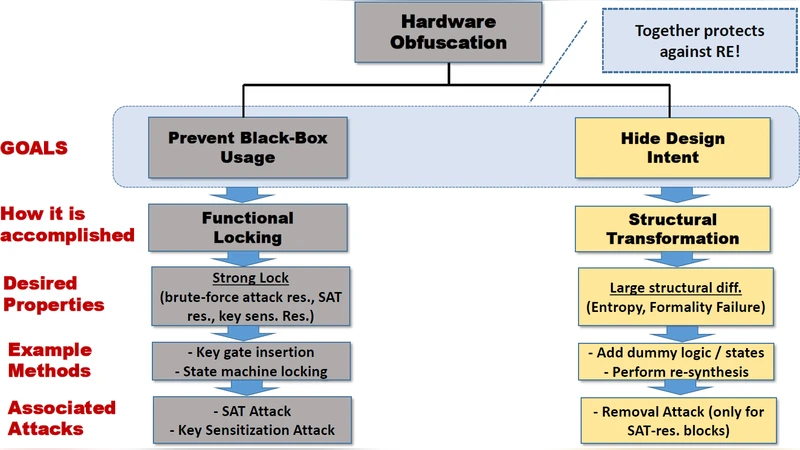
SAIL: Machine Learning Guided Structural Analysis Attack on Hardware Obfuscation
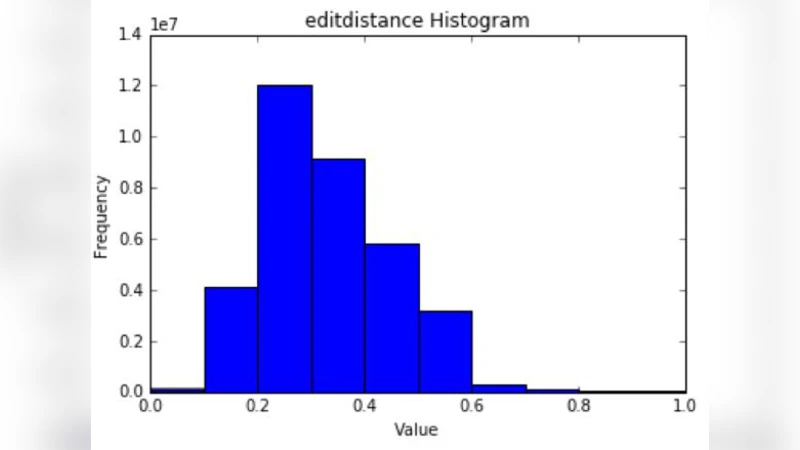
The Evolution of User-Selected Passwords: A Quantitative Analysis of Publicly Available Datasets
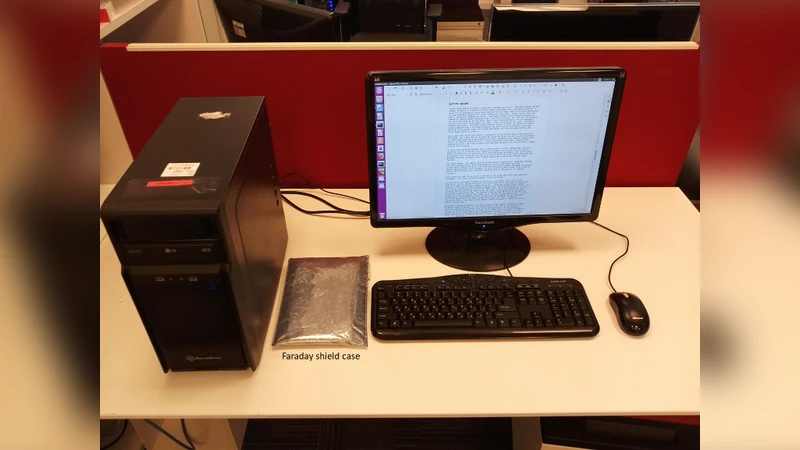
MAGNETO: Covert Channel between Air-Gapped Systems and Nearby Smartphones via CPU-Generated Magnetic Fields

Distributed Random Number Generation for the Needs of Public Governance

A SDN-based Flexible System for On-the-Fly Monitoring and Treatment of Security Events
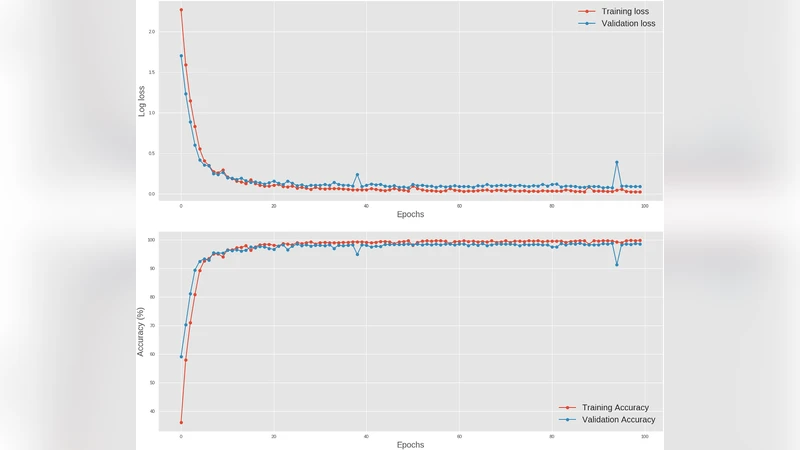
Deep learning at the shallow end: Malware classification for non-domain experts
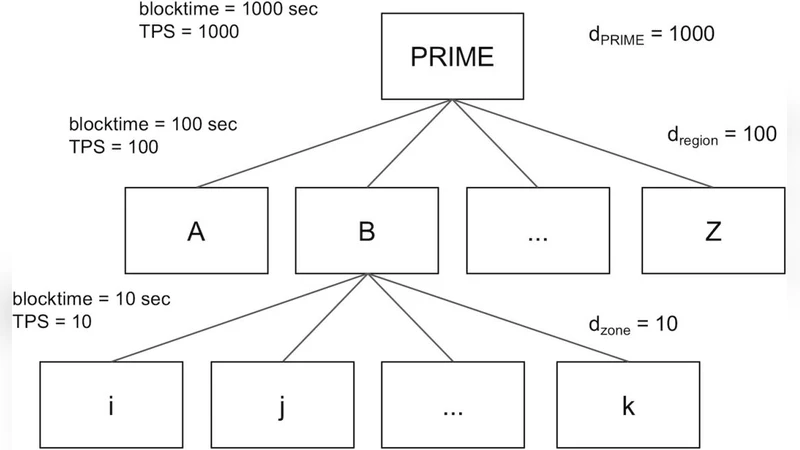
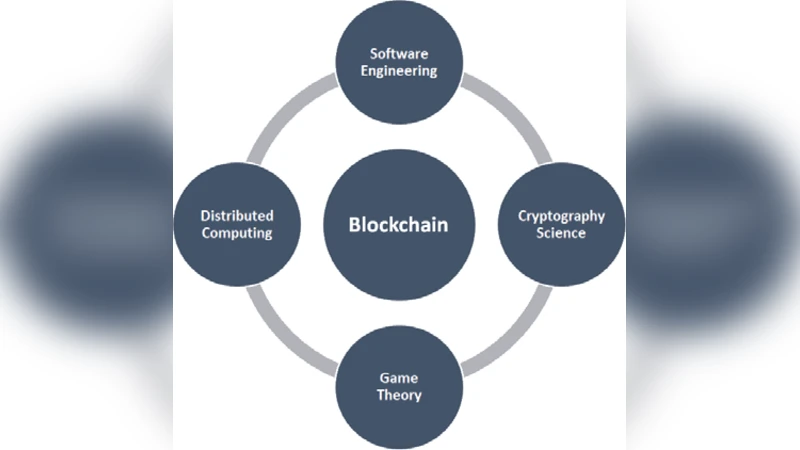
BlockReduce: Scaling Blockchain to Human Commerce

A First Look at Identity Management Schemes on the Blockchain
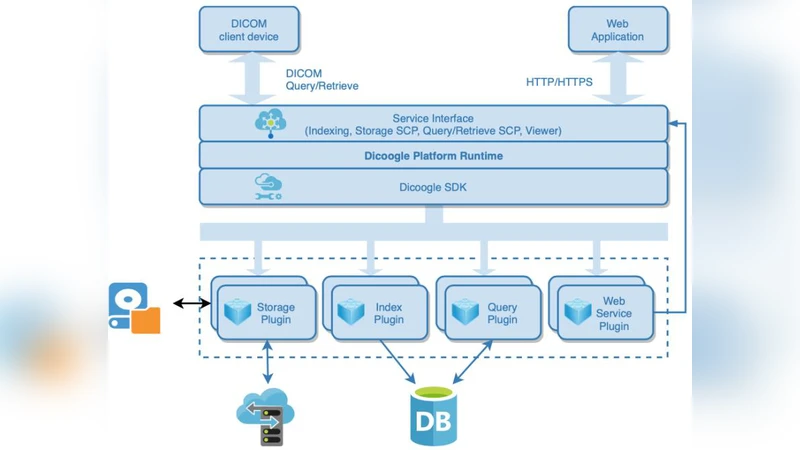
A Cloud-ready Architecture for Shared Medical Imaging Repository

Leveraging Machine Learning Techniques for Windows Ransomware Network Traffic Detection
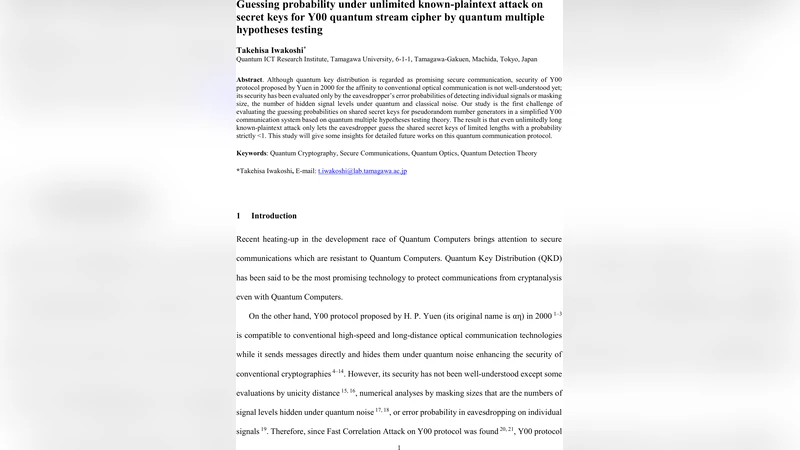
Guessing probability under unlimited known-plaintext attack on secret keys for Y00 quantum stream cipher by quantum multiple hypotheses testing

A Novel Trigon based Dual Authentication Protocol for Enhancing Security in Grid Environment

Application of Lowner-John Ellipsoid in the Steganography of Lattice Vectors and a Review of The Gentrys FHE
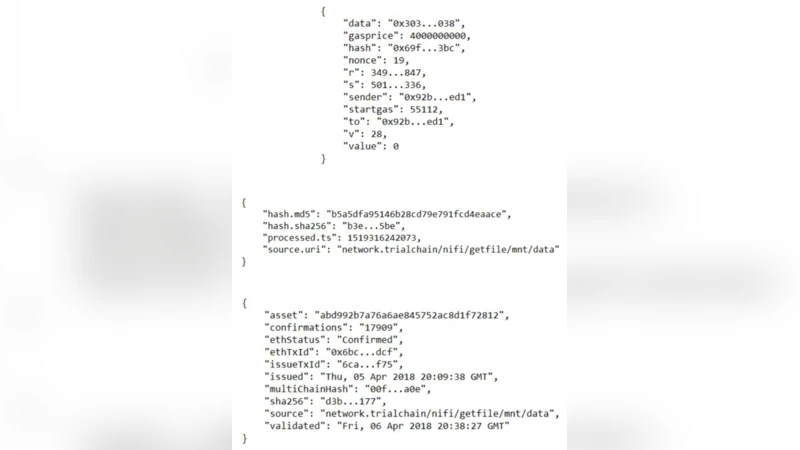
TrialChain: A Blockchain-Based Platform to Validate Data Integrity in Large, Biomedical Research Studies

CloudMe Forensics: A Case of Big-Data Investigation
A Robust and Efficient Trust Management Scheme for Peer-to-Peer Networks

Intrusion Prediction with System-call Sequence-to-Sequence Model

On Critical Infrastructures, Their Security and Resilience - Trends and Vision
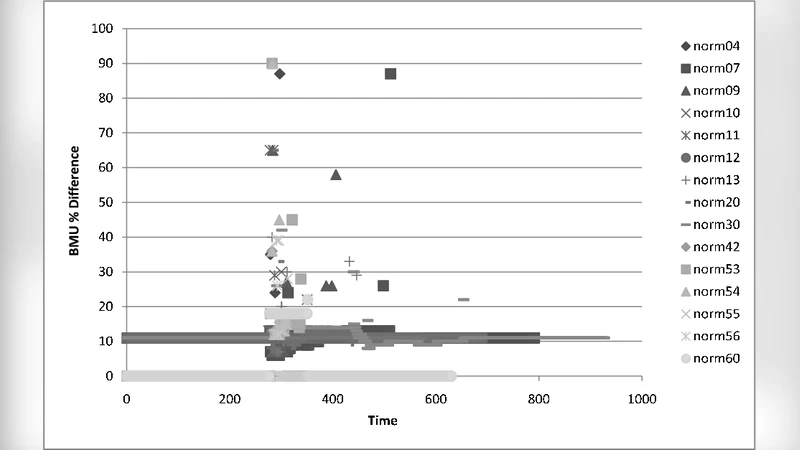
ToLeRating UR-STD

Image Encryption Using Differential Evolution Approach in Frequency Domain
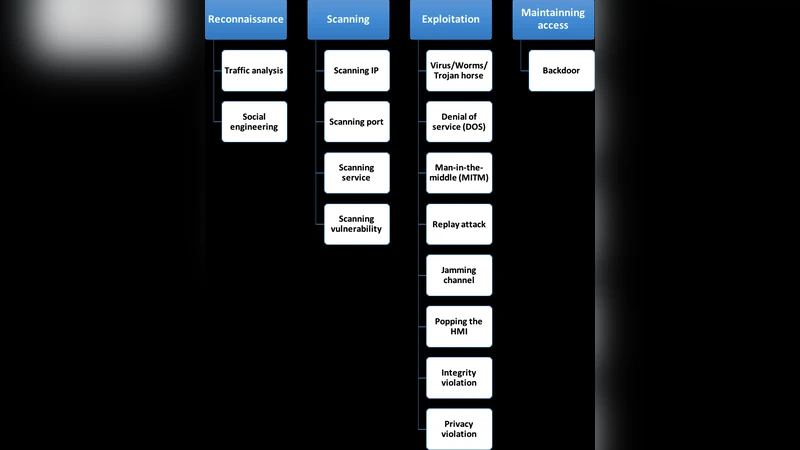
Cyber-Security in Smart Grid: Survey and Challenges
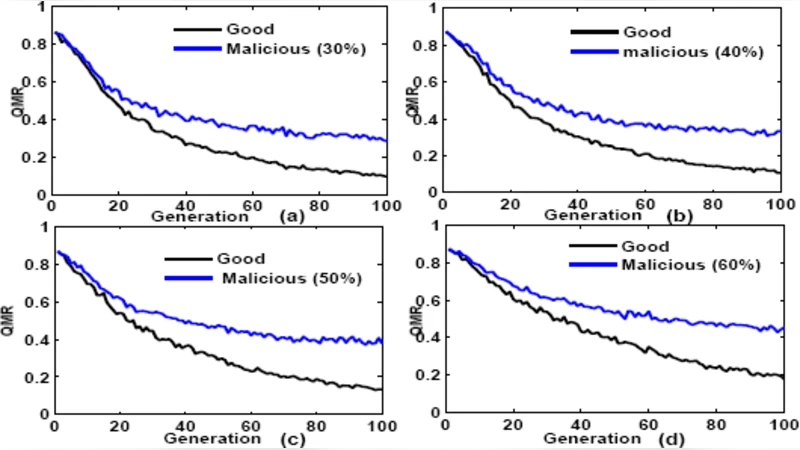
An Effective Privacy-Preserving Data Coding in Peer-To-Peer Network