Cs-Cr

Binary Random Sequences Obtained From Decimal Sequences

Finding matching initial states for equivalent NLFSRs in the fibonacci and the galois configurations
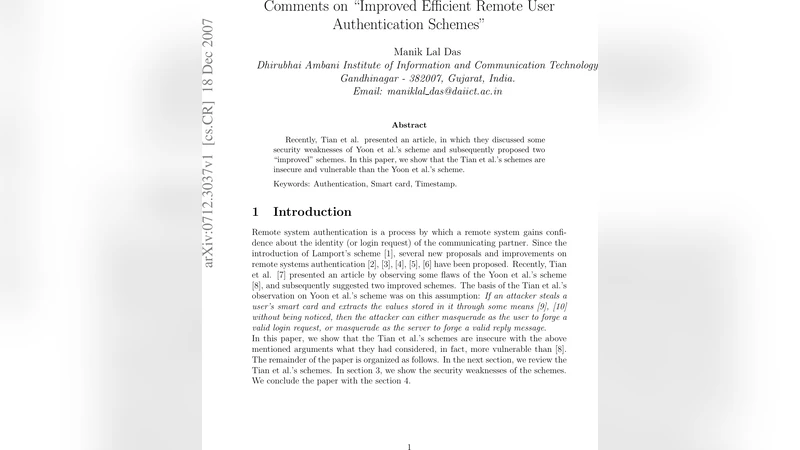
Comments on "Improved Efficient Remote User Authentication Schemes"

GSM Security Using Identity-based Cryptography
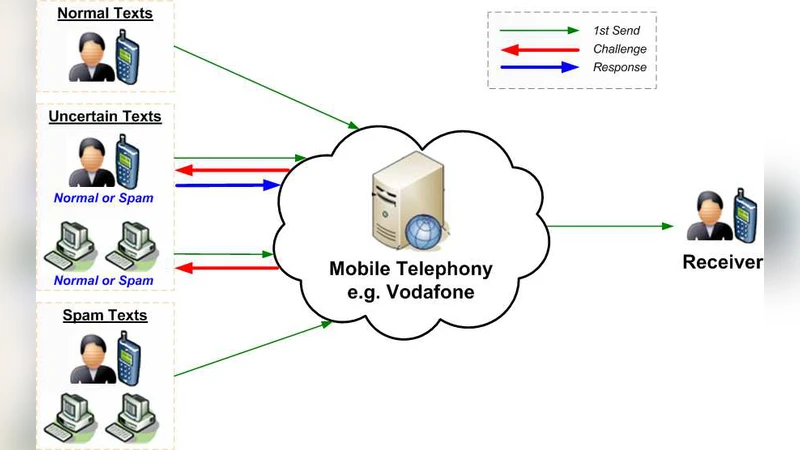
Hybrid Spam Filtering for Mobile Communication

Some A Priori Torah Decryption Principles

A chaos-based approach for information hiding security

Lightweight Security for Network Coding

Privately Releasing Conjunctions and the Statistical Query Barrier

Cryptanalysis of an Image Encryption Scheme Based on a Compound Chaotic Sequence

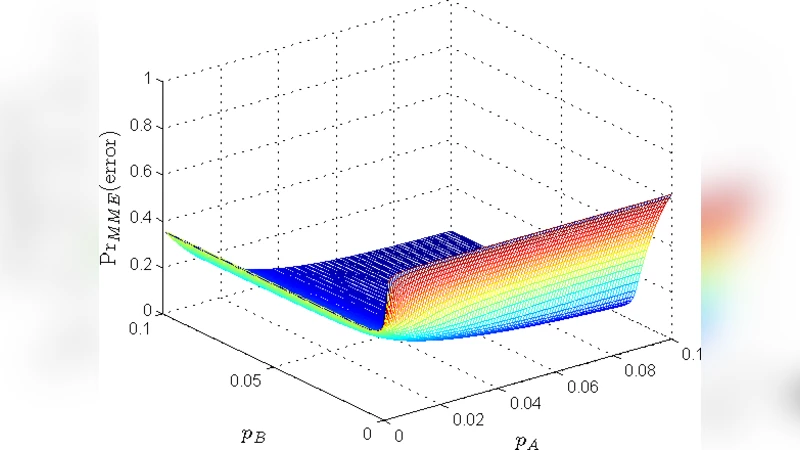
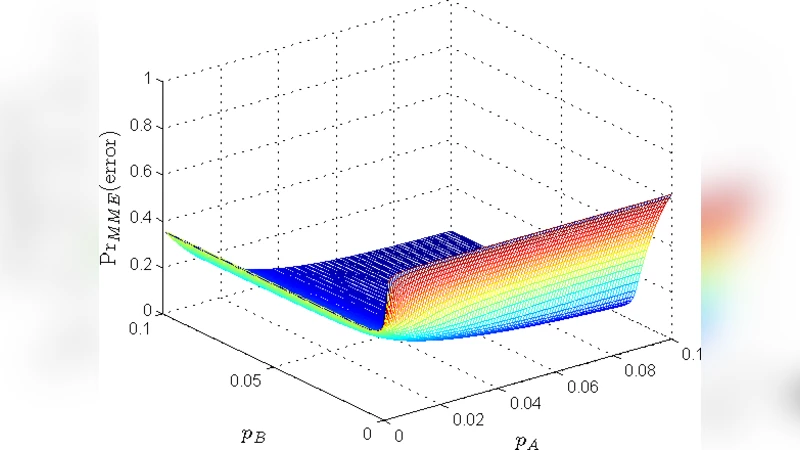
On the Performance of Joint Fingerprint Embedding and Decryption Scheme

On the Protocol Composition Logic PCL
Quasigroups in cryptology
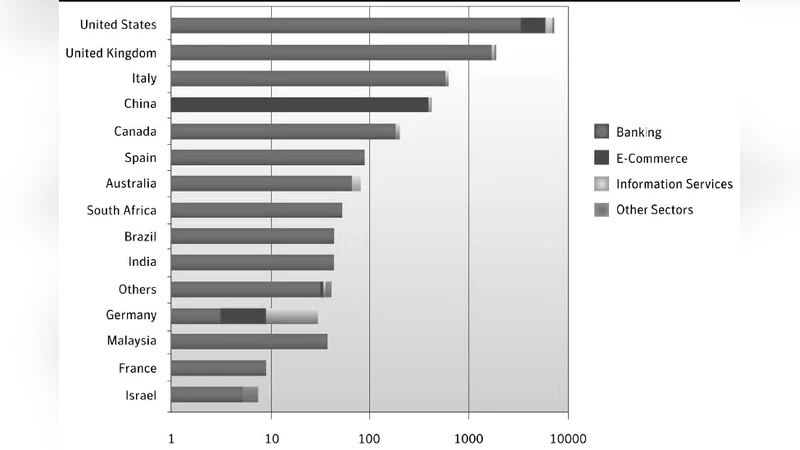
Securite des syst`emes critiques et cybercriminalite : vers une securite globale ?
On the AAGL Protocol
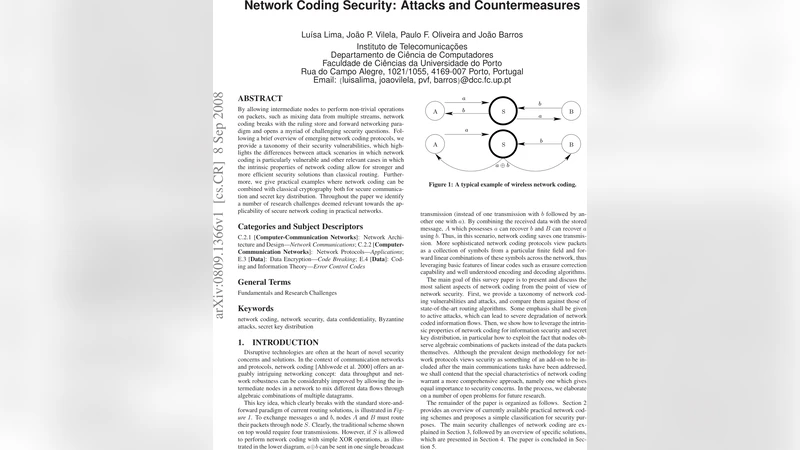
Network Coding Security: Attacks and Countermeasures

Quantum Measurements Cannot be Proved to be Random
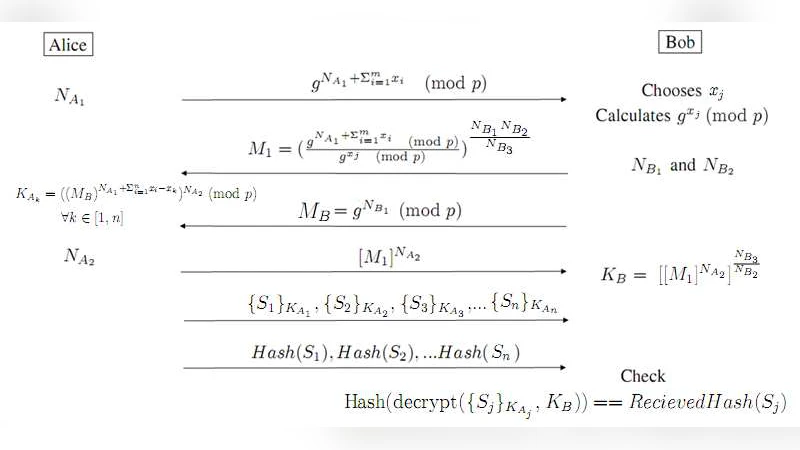
A new efficient k-out-of-n Oblivious Transfer protocol
Case Study On Social Engineering Techniques for Persuasion
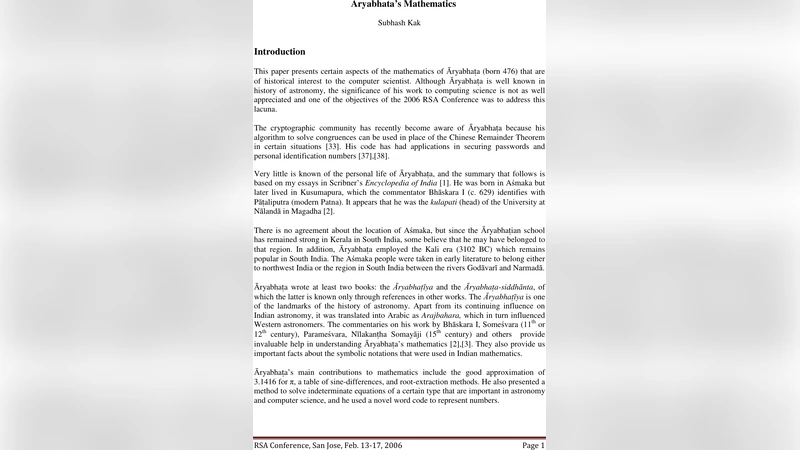
Aryabhatas Mathematics

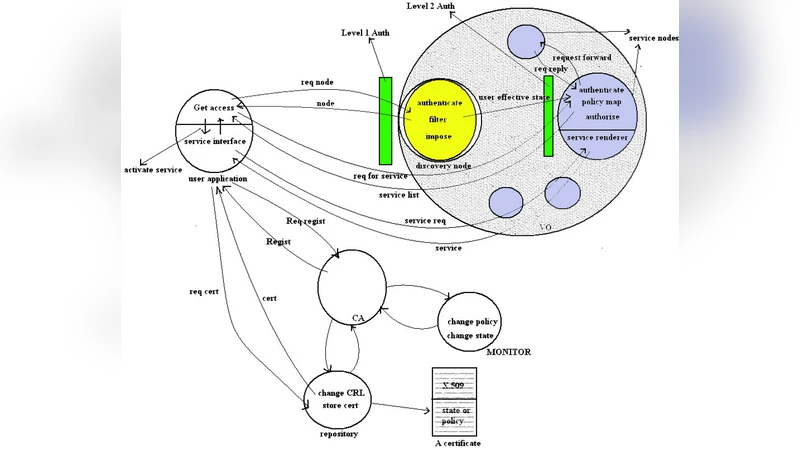
Common Representation of Information Flows for Dynamic Coalitions
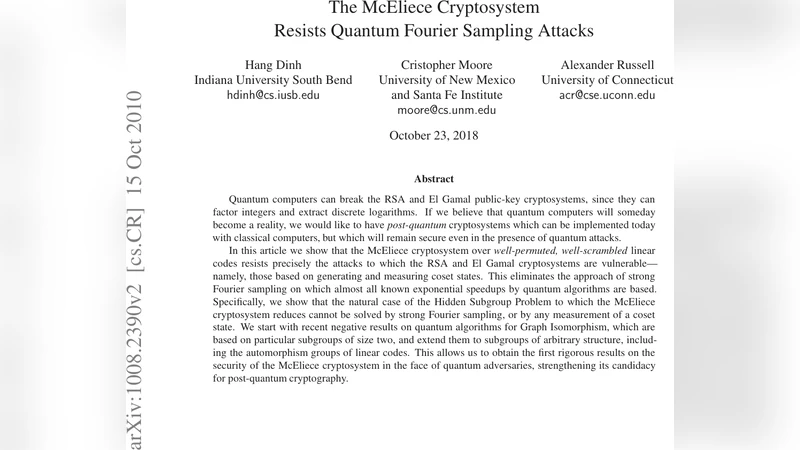
The McEliece Cryptosystem Resists Quantum Fourier Sampling Attacks