Cs-Cr

General Hardness Amplification of Predicates and Puzzles
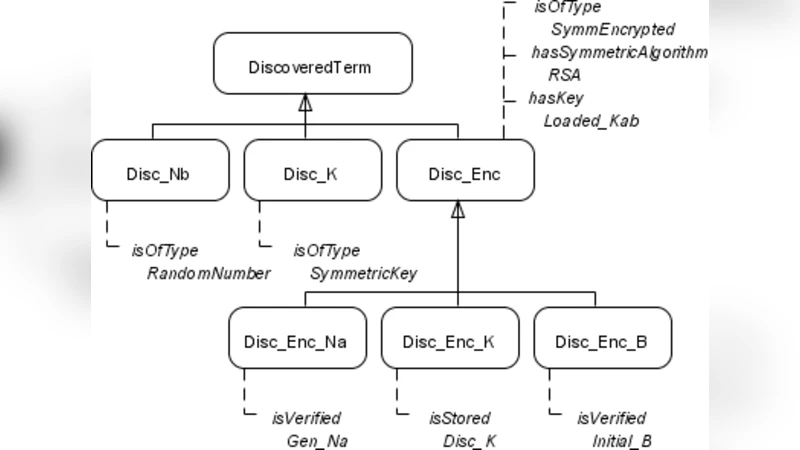
A Modeling Framework for Generating Security Protocol Specifications

Safer in the Clouds (Extended Abstract)

Cryptanalysis of group-based key agreement protocols using subgroup distance functions
Design and Analysis of an Attack Resilient and Adaptive Medium access Control Protocol for Computer Networks
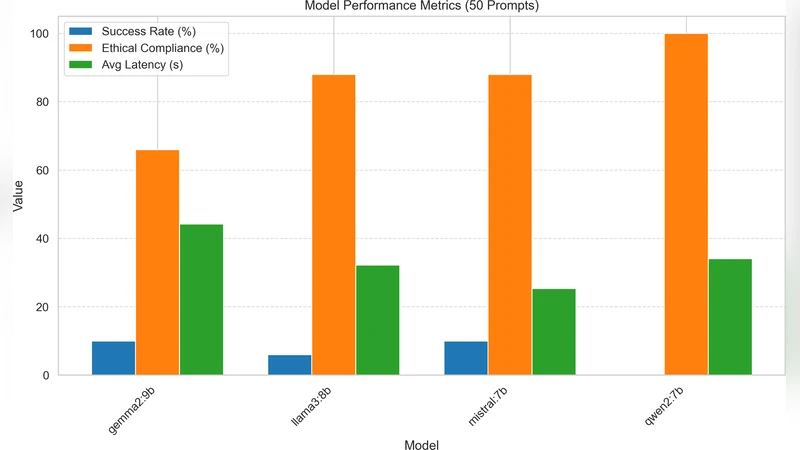
Emoji-Based Jailbreaking of Large Language Models
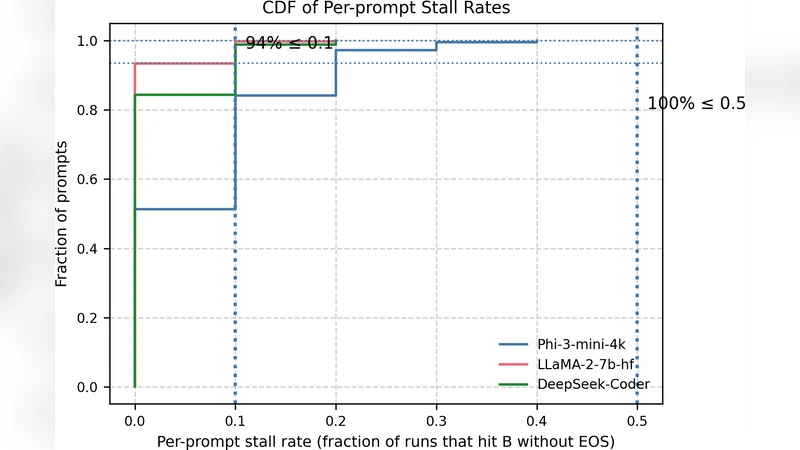
Prompt-Induced Over-Generation as Denial-of-Service: A Black-Box Attack-Side Benchmark
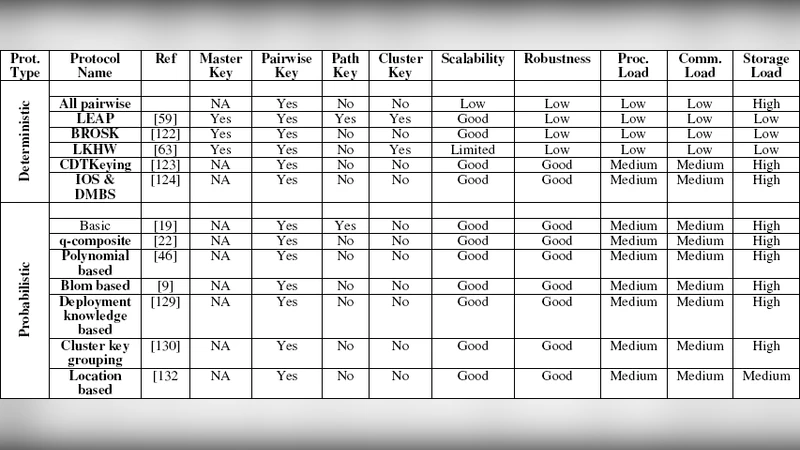
A Survey on Wireless Sensor Network Security
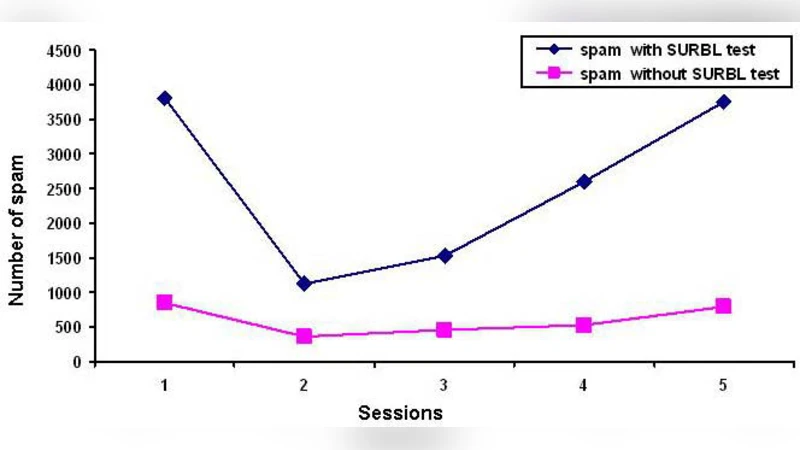
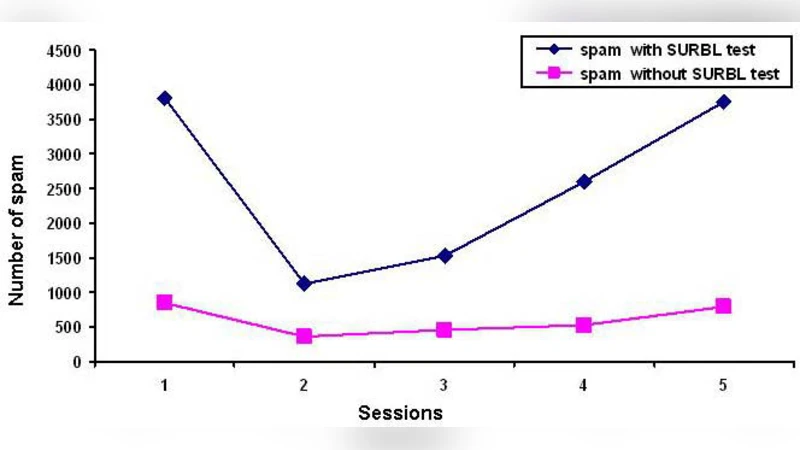
A secure email login system using virtual password
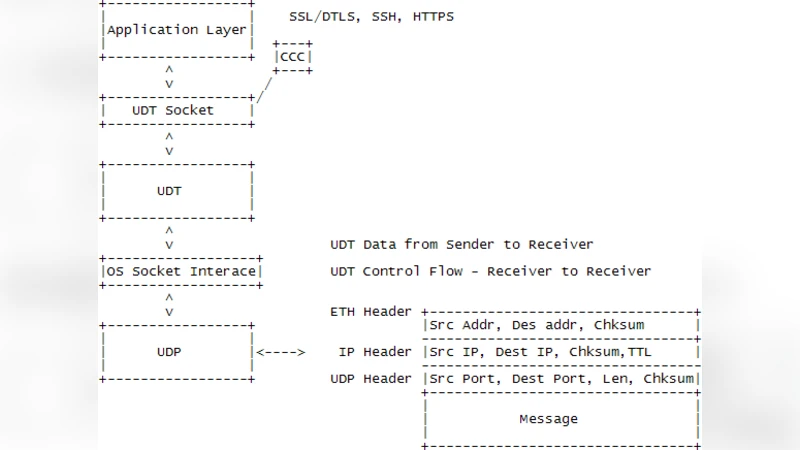
Securing data transfer in the cloud through introducing identification packet and UDT-authentication option field: a characterization
Anti-Collusion Digital Fingerprinting Codes via Partially Cover-Free Families

Reducing Protocol Analysis with XOR to the XOR-free Case in the Horn Theory Based Approach
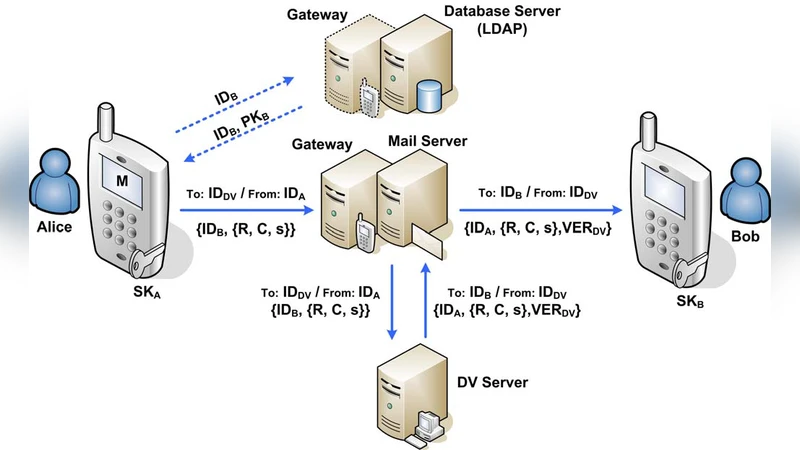
SMEmail - A New Protocol for the Secure E-mail in Mobile Environments
Nation-State Routing: Censorship, Wiretapping, and BGP

Theory of Rumour Spreading in Complex Social Networks

The Asymptotic Normalized Linear Complexity of Multisequences
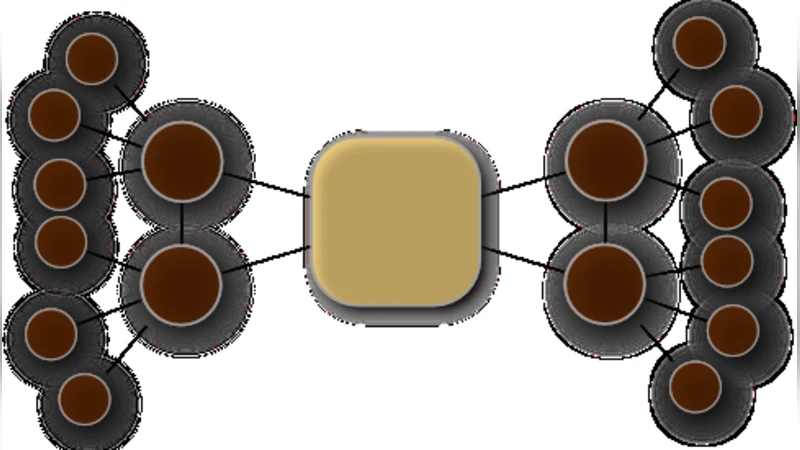
Constrained Function Based En-Route Filtering for Sensor Networks

Position-Based Quantum Cryptography: Impossibility and Constructions
A Survey of Biometric keystroke Dynamics: Approaches, Security and Challenges

Feedback-Based Collaborative Secrecy Encoding over Binary Symmetric Channels
Consideration Points Detecting Cross-Site Scripting
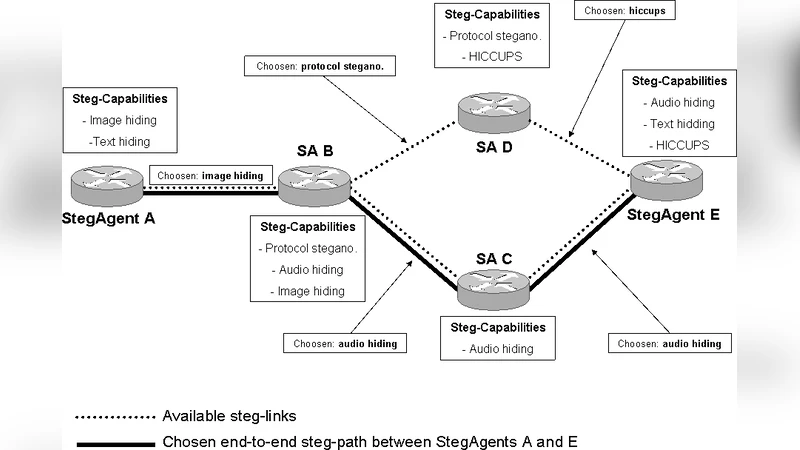
TrustMAS: Trusted Communication Platform for Multi-Agent Systems