Cs-Cr

IRONHIDE: A Secure Multicore that Efficiently Mitigates Microarchitecture State Attacks for Interactive Applications

Reversible Data Hiding in Encrypted Images using Local Difference of Neighboring Pixels

Double Blind Comparisons using Groups with Infeasible Inversion
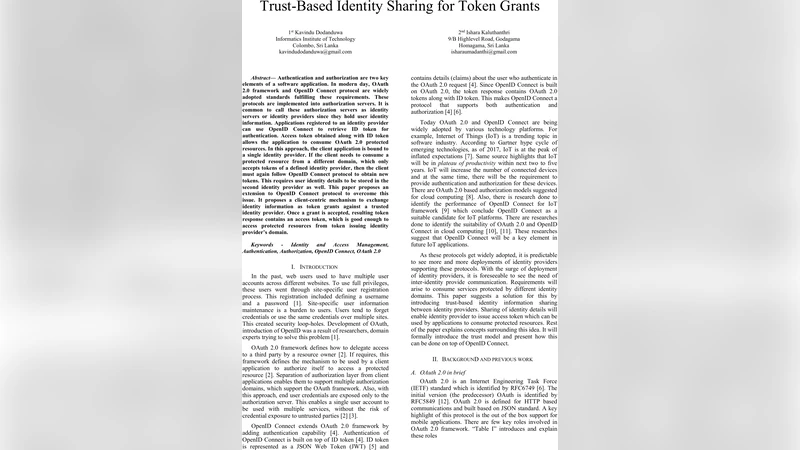
Trust-Based Identity Sharing For Token Grants

Can Blockchain Protect Internet-of-Things?
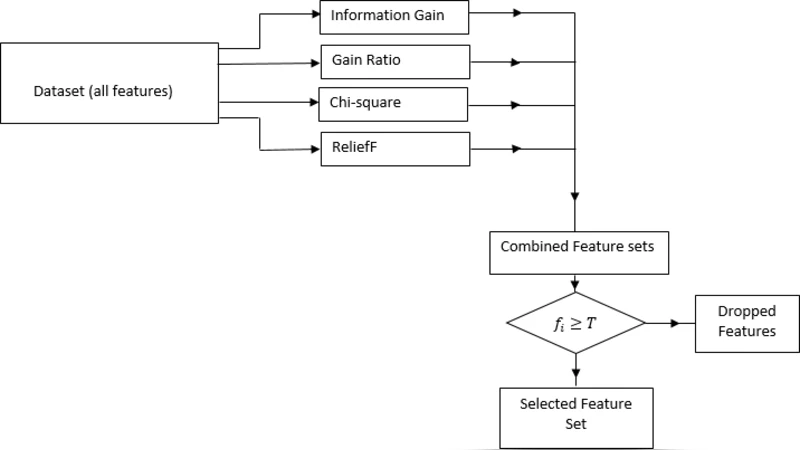
Ensemble-based Multi-Filter Feature Selection Method for DDoS Detection in Cloud Computing

Transformation from Identity Stone Age to Digital Identity
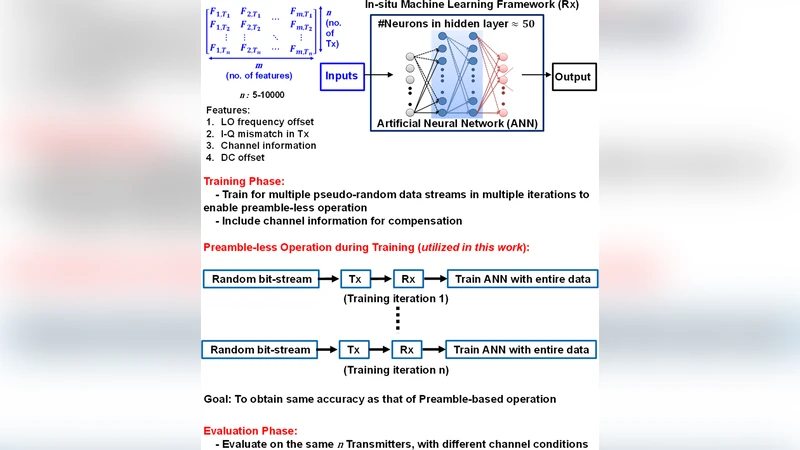
RF-PUF: Enhancing IoT Security through Authentication of Wireless Nodes using In-situ Machine Learning
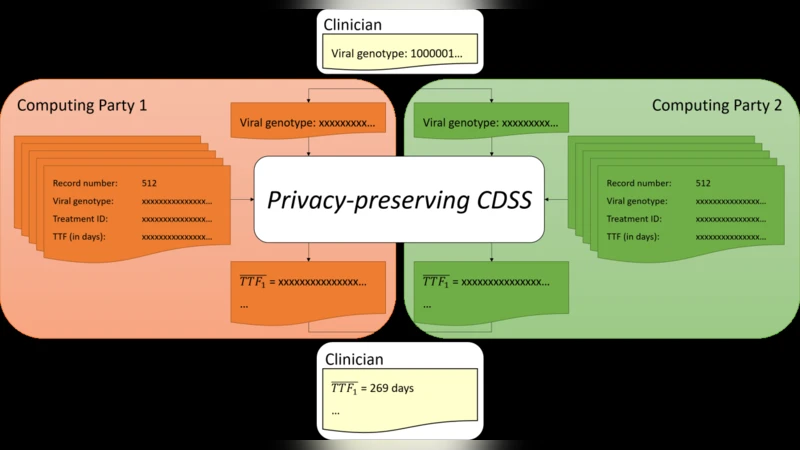
A New Approach to Privacy-Preserving Clinical Decision Support Systems
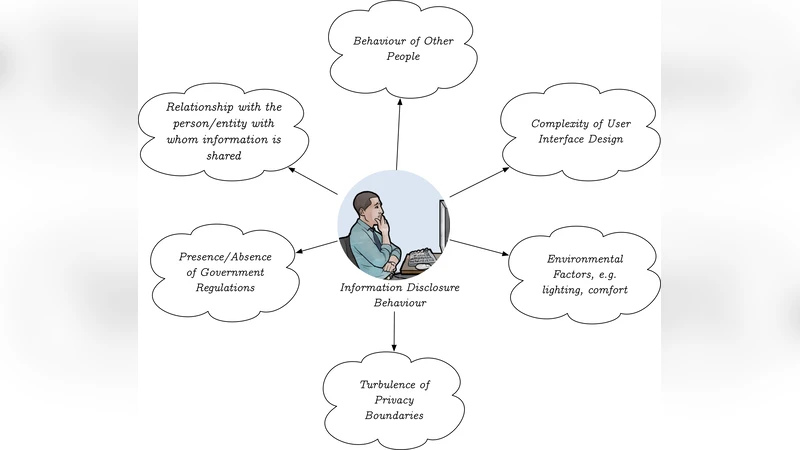
Human Aspects and Perception of Privacy in Relation to Personalization

Shakedown: compiler-based moving target protection for Return Oriented Programing attacks on an industrial IoT device
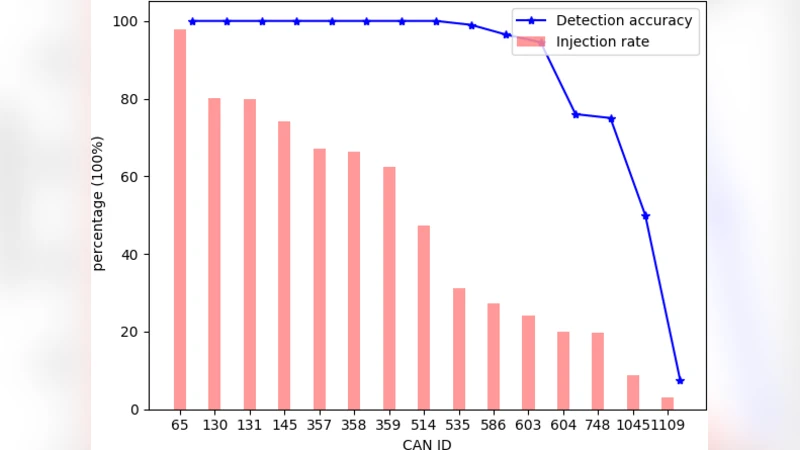
An Entropy Analysis based Intrusion Detection System for Controller Area Network in Vehicles
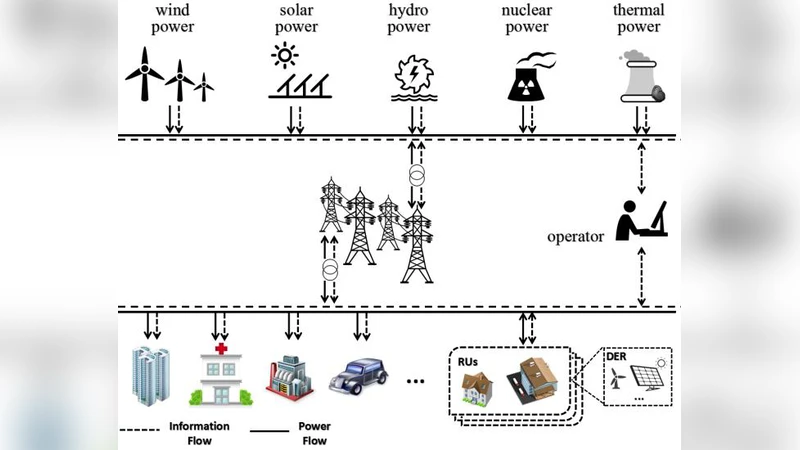
Towards Delay-Tolerant Flexible Data Access Control for Smart Grid with Renewable Energy Resources

A Framework for Data-Driven Physical Security and Insider Threat Detection
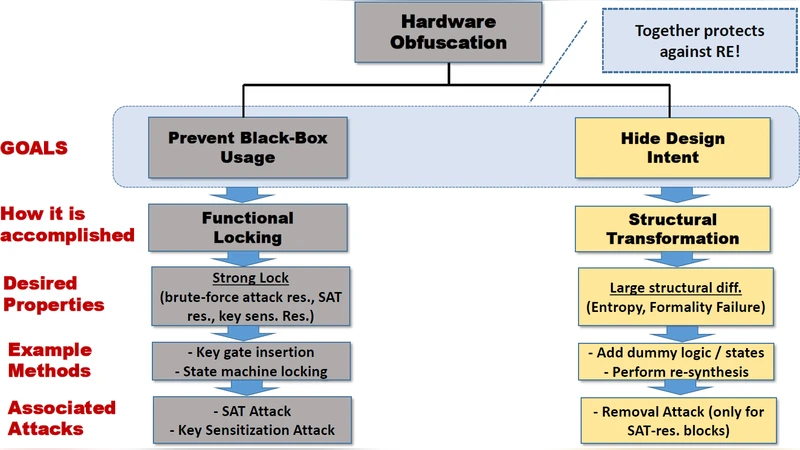
SAIL: Machine Learning Guided Structural Analysis Attack on Hardware Obfuscation
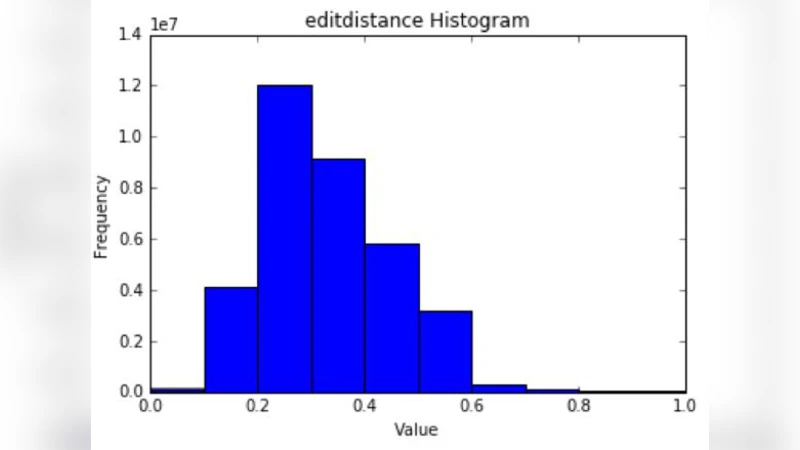
The Evolution of User-Selected Passwords: A Quantitative Analysis of Publicly Available Datasets
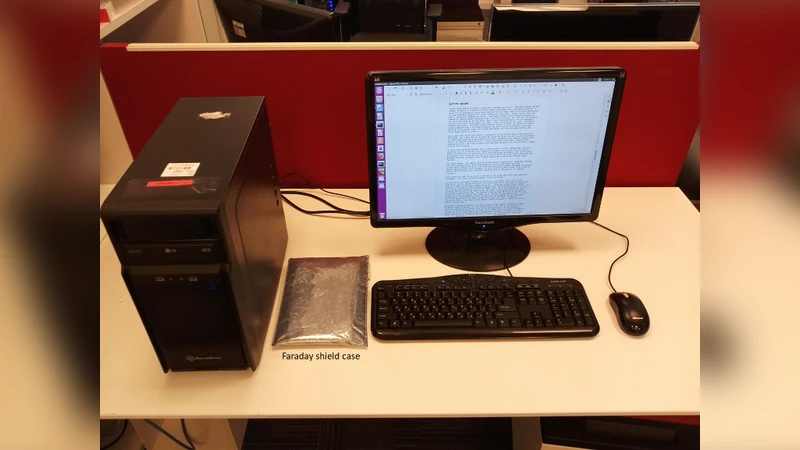
MAGNETO: Covert Channel between Air-Gapped Systems and Nearby Smartphones via CPU-Generated Magnetic Fields

Distributed Random Number Generation for the Needs of Public Governance

A SDN-based Flexible System for On-the-Fly Monitoring and Treatment of Security Events
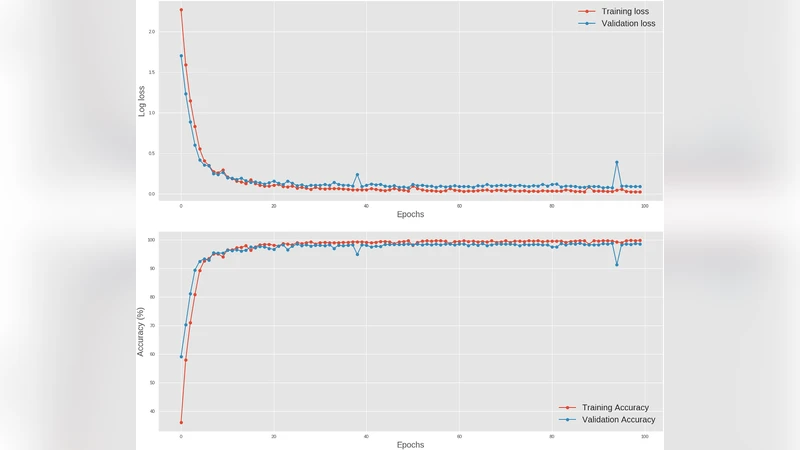
Deep learning at the shallow end: Malware classification for non-domain experts
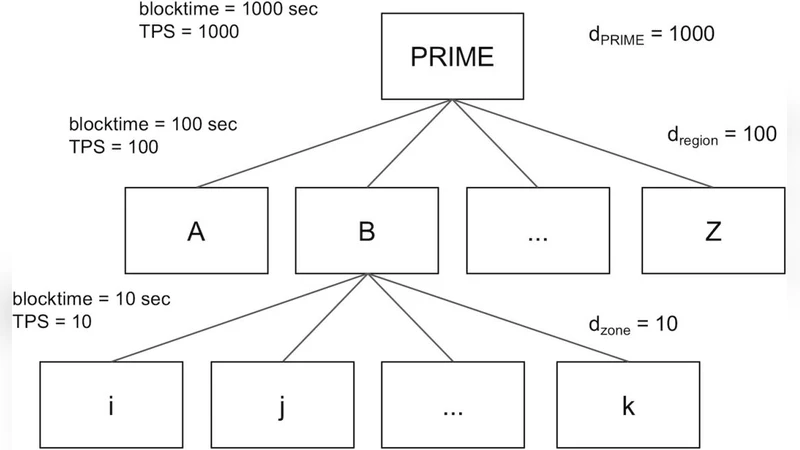
BlockReduce: Scaling Blockchain to Human Commerce

A First Look at Identity Management Schemes on the Blockchain