
Cs-Cr

Lossless Secret Image Sharing Schemes
MARFCAT: Transitioning to Binary and Larger Data Sets of SATE IV
Modeling and performance evaluation of computer systems security operation
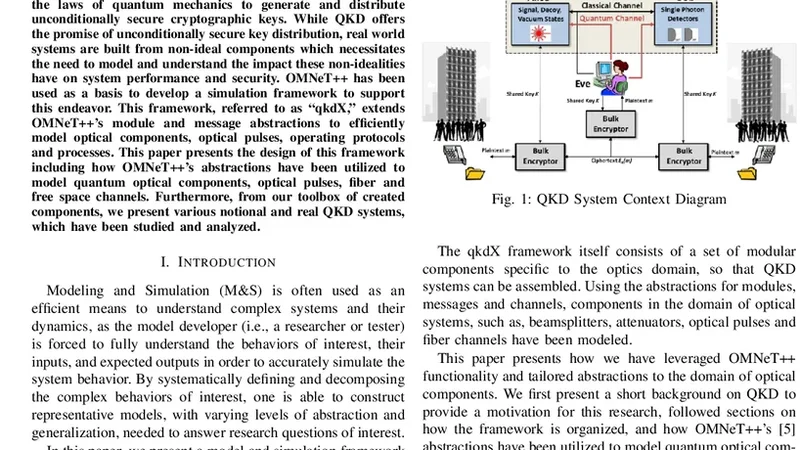
Modeling Quantum Optical Components, Pulses and Fiber Channels Using OMNeT++
Modified Trial Division Algorithm Using KNJ-Factorization Method To Factorize RSA Public Key Encryption
Multi-phase IRC Botnet and Botnet Behavior Detection Model
Multi-terminal Secrecy in a Linear Non-coherent Packetized Networks
New Hashing Algorithm for Use in TCP Reassembly Module of IPS
New Parameters of Linear Codes Expressing Security Performance of Universal Secure Network Coding
On Side Channel Cryptanalysis and Sequential Decoding

On the security of an enhanced short signature scheme

On the Use of Latency Graphs for the Construction of Tor Circuits
On-the fly AES Decryption/Encryption for Cloud SQL Databases
Optimized Password Recovery for Encrypted RAR on GPUs
Parameter security characterization of knapsack public-key crypto under quantum computing
Phishing Detection in IMs using Domain Ontology and CBA - An innovative Rule Generation Approach
Practical Solutions For Format-Preserving Encryption
Preventing SQL Injection attack using pattern matching algorithm
Recovering Residual Forensic Data from Smartphone Interactions with Cloud Storage Providers
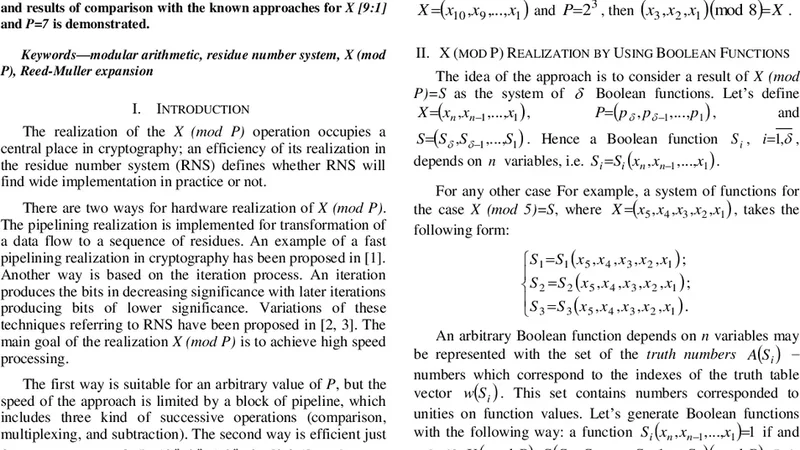
Reed-Muller Realization of X (mod P)
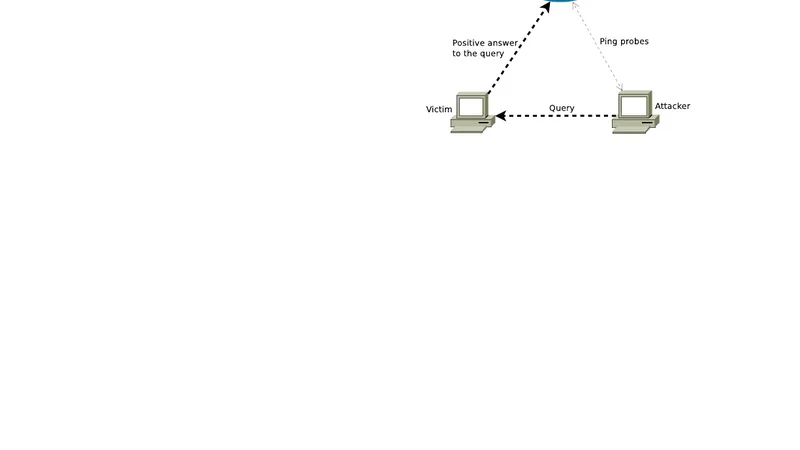
Reflection Scan: an Off-Path Attack on TCP

RFID Security Using Lightweight Mutual Authentication And Ownership Transfer Protocol
