Cs-Cr
Personal data disclosure and data breaches: the customers viewpoint

BotMosaic: Collaborative Network Watermark for Botnet Detection
A Novel Data Hiding Scheme for Binary Images

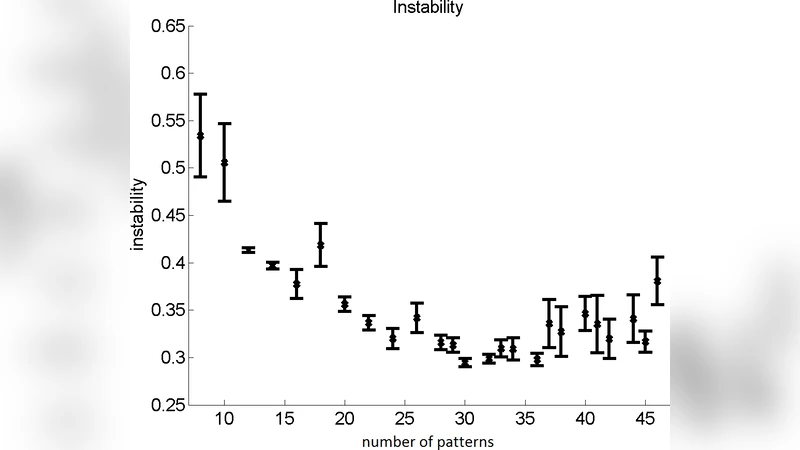
On Randomness of Goldbach Sequences
A Key Pre-Distribution Scheme based on Multiple Block Codes for Wireless Sensor Networks

Torsion Limits and Riemann-Roch Systems for Function Fields and Applications

Noninterference with Local Policies
Breaking a novel colour image encryption algorithm based on chaos
Stream on the Sky: Outsourcing Access Control Enforcement for Stream Data to the Cloud
Mining Permission Request Patterns from Android and Facebook Applications (extended author version)
A machine learning approach to anomaly-based detection on Android platforms
A Socio-Technical approach to address the Information security: Using the 27001 Manager Artefact
A Survey on Detection of Sinkhole Attack in Wireless Sensor Network
Breaking Bad: Detecting malicious domains using word segmentation
Image encryption schemes for JPEG and GIF formats based on 3D baker with compound chaotic sequence generator
Minimizing the Time of Detection of Large (Probably) Prime Numbers
Non-profit Organizations Need to Address Security for Effective Government Contacting

Privacy and Data Protection by Design - from policy to engineering
Privacy and the City: User Identification and Location Semantics in Location-Based Social Networks
Recommendations on Future Operational Environments Command Control and Cyber Security
Research on Anonymization and De-anonymization in the Bitcoin System

Secure Transmission in Wireless Sensor Networks Data Using Linear Kolmogorov Watermarking Technique