
Cs-Cr


No SQL, No Injection? Examining NoSQL Security

A novel approach against E-mail attacks derived from user-awareness based techniques

A short note on the kissing number of the lattice in Gaussian wiretap coding
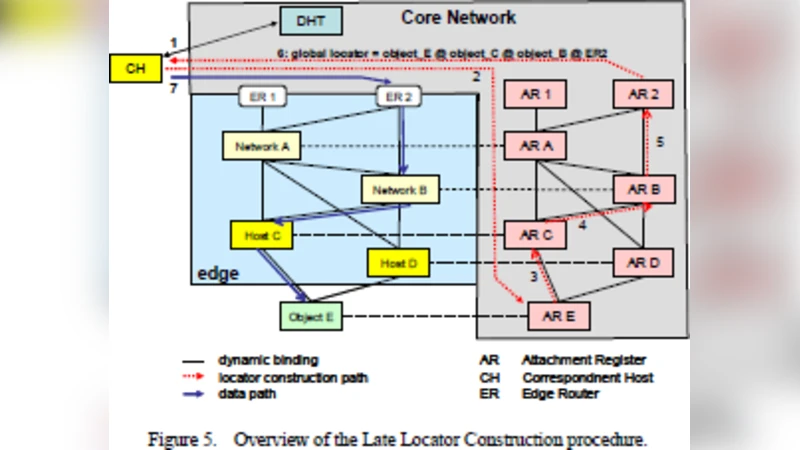
An Effective Fusion Technique of Cloud Computing and Networking Series

The 2008 Australian study of remnant data contained on 2nd hand hard disks: the saga continues

The Metadata Anonymization Toolkit

Accelerating Iterative SpMV for Discrete Logarithm Problem Using GPUs

Linear Transformations for Randomness Extraction
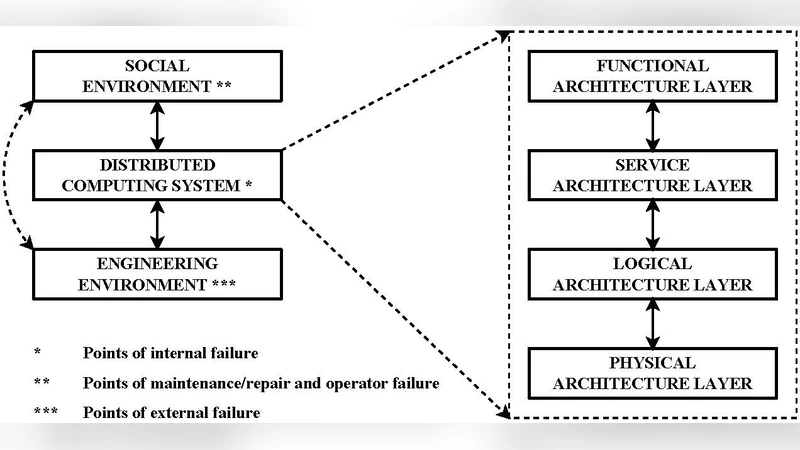
A Formal Approach to Distributed System Security Test Generation

Differential Spectrum of Some Power Functions With Low Differential Uniformity
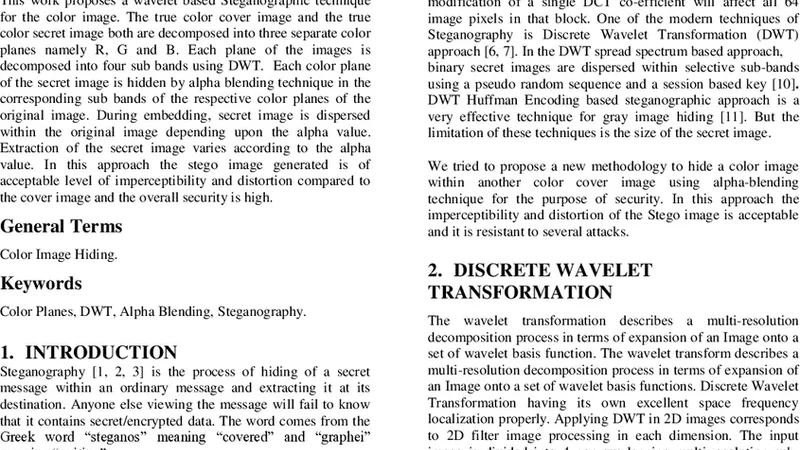
A Novel Approach of Color Image Hiding using RGB Color planes and DWT

A General Approach for Securely Querying and Updating XML Data
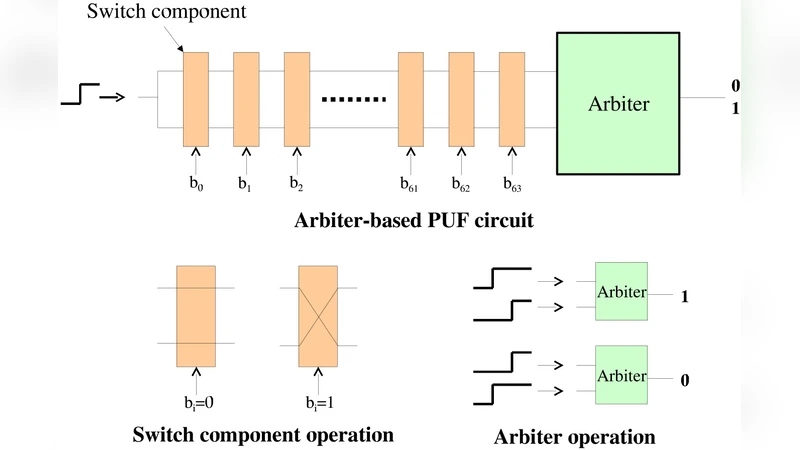
Physical Unclonable Function (PUF) Based Random Number Generator

Simple and Efficient Contract Signing Protocol
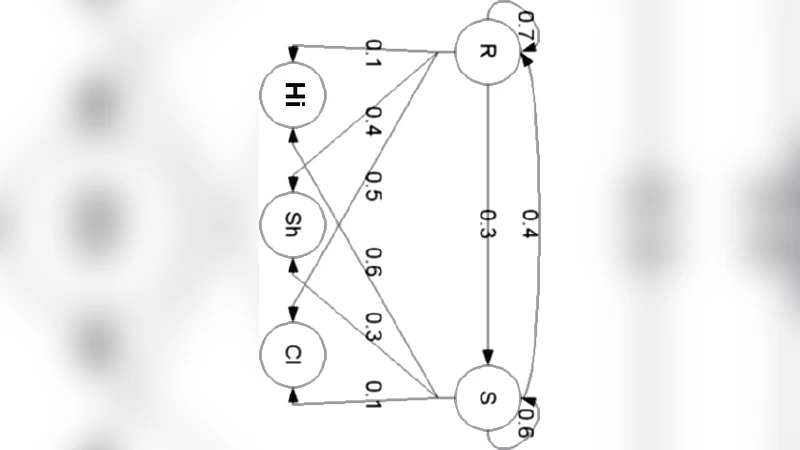
Security issues for data sharing and service interoperability in eHealth systems: the Nu.Sa. test bed
The Hush Cryptosystem

Pairing-based algorithms for jacobians of genus 2 curves with maximal endomorphism ring
CAWS - Security Algorithms for Wireless Sensor Networks: A Cellular Automata Based Approach

Symbolic Protocol Analysis for Diffie-Hellman

Integrated Key based Strict Friendliness Verification of Neighbors in MANET

Globally reasoning about localised security policies in distributed systems

Deducing Security Goals From Shape Analysis Sentences
