Cs-Cr

Public Key Cryptography Standards: PKCS
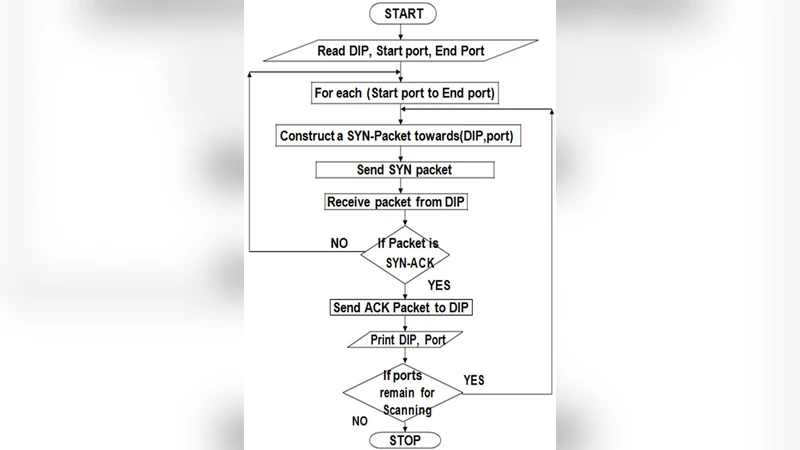
Scanning of Rich Web Applications for Parameter Tampering Vulnerabilities

Auditing for Distributed Storage Systems
High Security Image Steganography with Modified Arnold cat map
Securing the Data in Clouds with Hyperelliptic Curve Cryptography
A Novel Approach to Detect Spam Worms Propagation with Monitoring the Footprinting
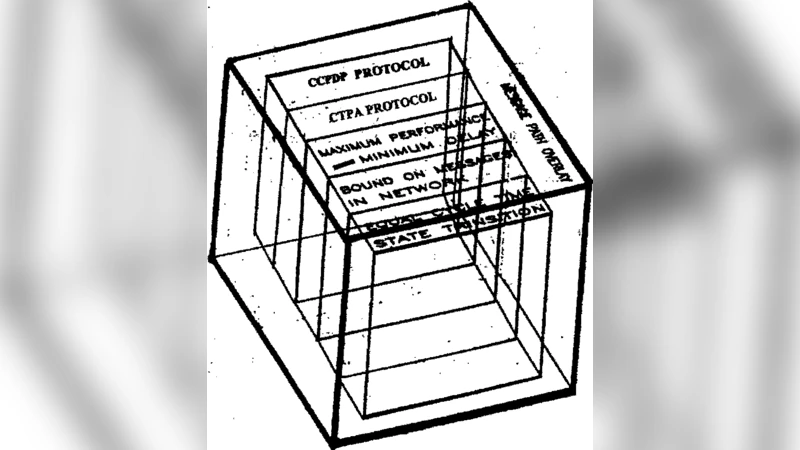
Homeland Defense and Security Universal Interface Software (HDUIS) Protocol Communication Gateway UIS Protocol Enhancements, Alterations and Attachments
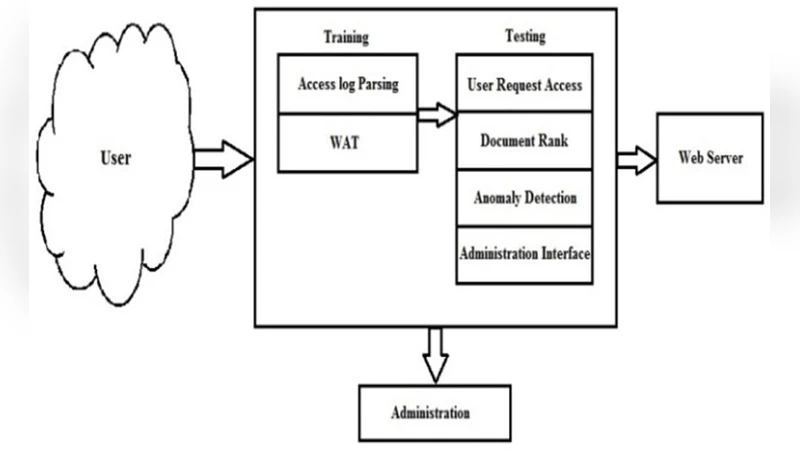
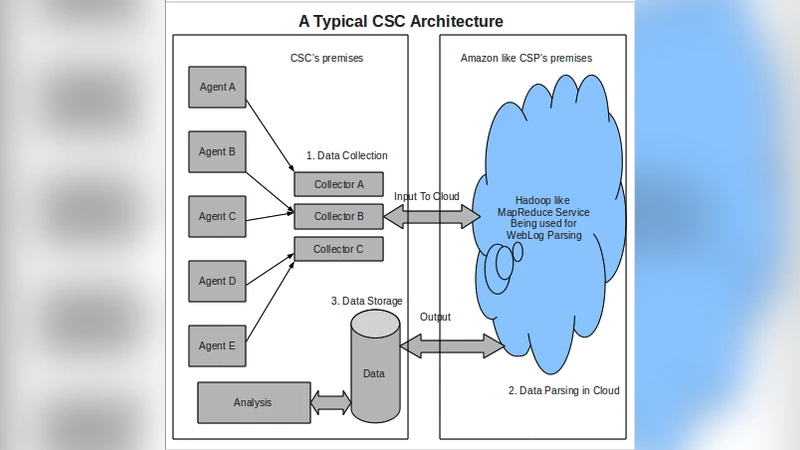
Anomaly Detection Based on Access Behavior and Document Rank Algorithm
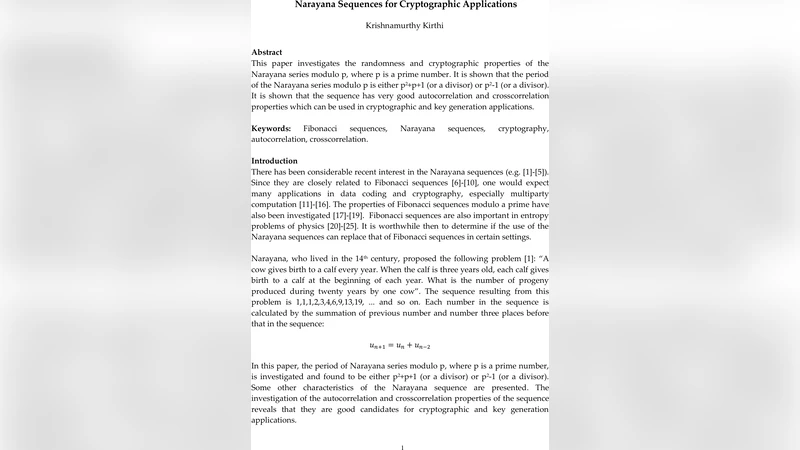
Narayana Sequences for Cryptographic Applications
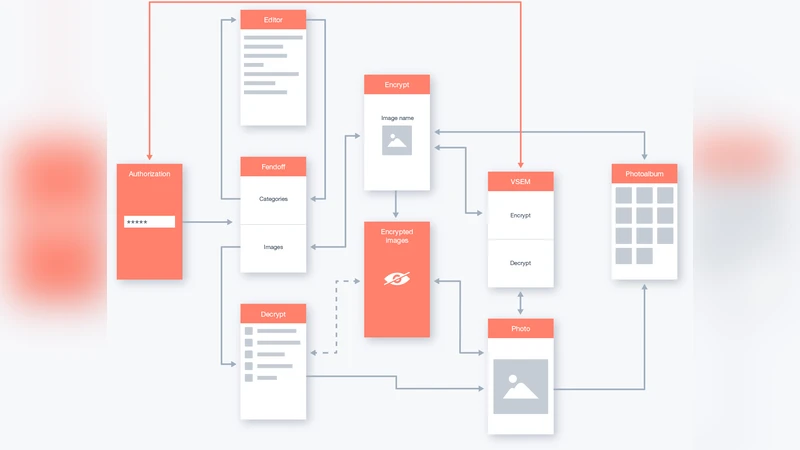
FendOff encryption software to secure personal information on computers and mobile devices
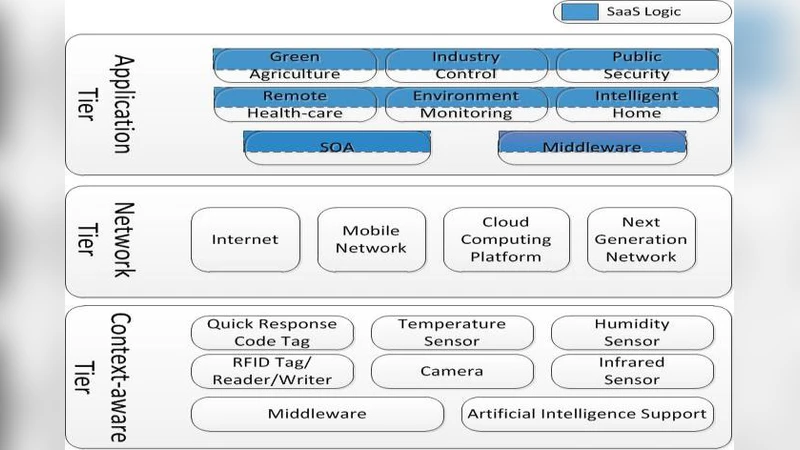
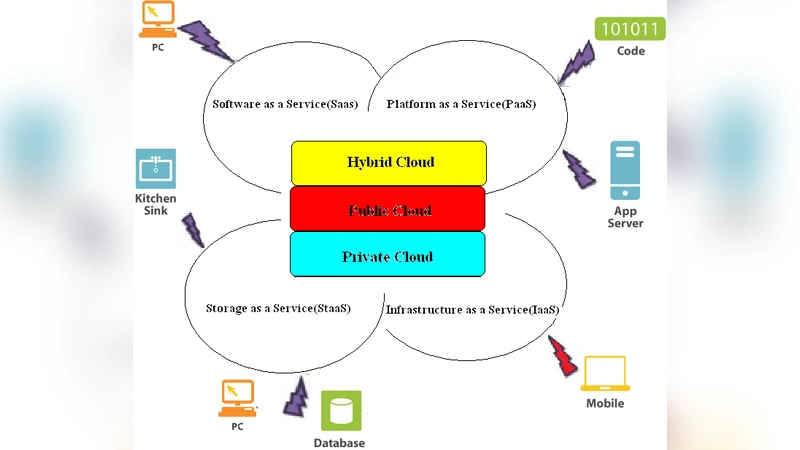
Software as a Service: Analyzing Security Issues
Classification of Various Security Techniques in Databases and their Comparative Analysis
Epistemic Temporal Logic for Information Flow Security

Ring Oscillator Physical Unclonable Function with Multi Level Supply Voltages
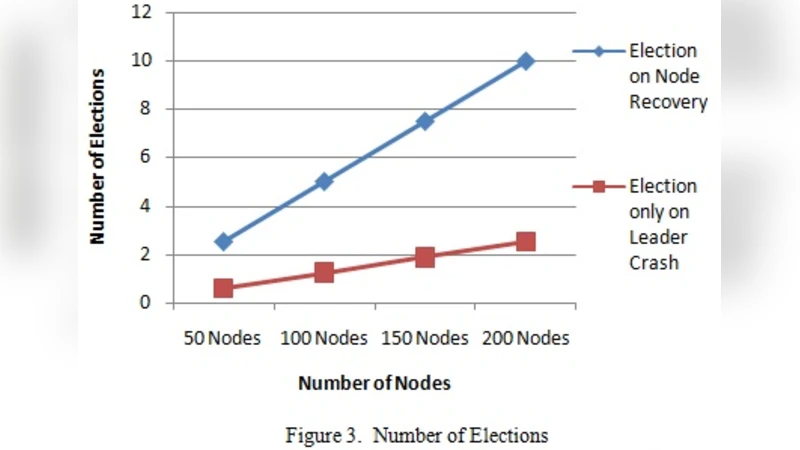
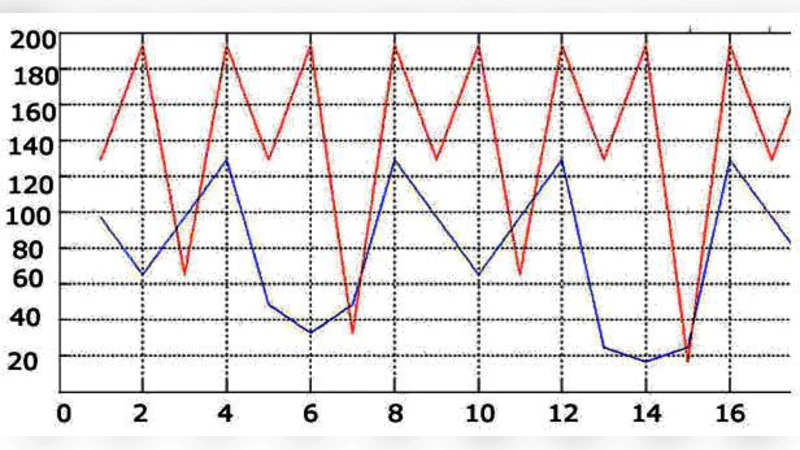
Analysis and Enhancements of Leader Elections algorithms in Mobile Ad Hoc Networks

Recovering Missing Coefficients in DCT-Transformed Images
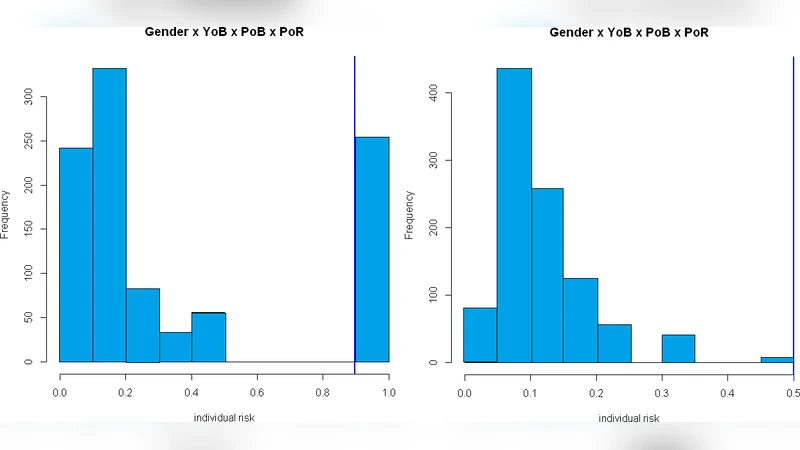
An experimental evaluation of de-identification tools for electronic health records
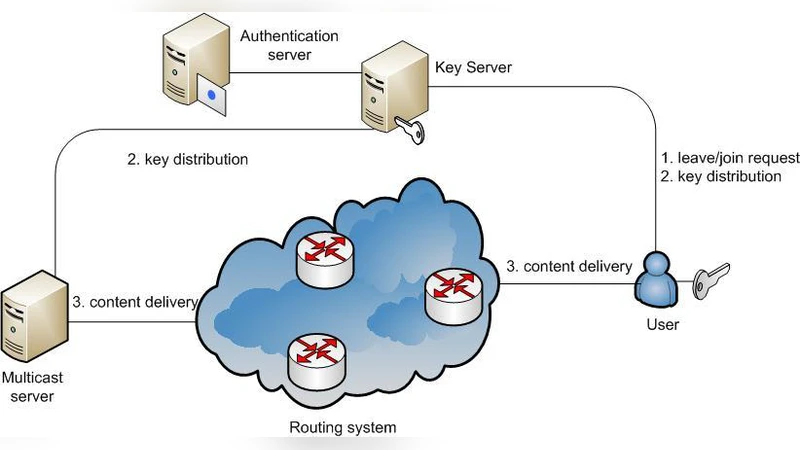
Efficient Group Key Management Schemes for Multicast Dynamic Communication Systems

Goldbach Triples and Key Distribution
Cryptographic Path Hardening: Hiding Vulnerabilities in Software through Cryptography
Confidentiality without Encryption For Cloud Computational Privacy

Genetic Programming for Multibiometrics