Cs-Cr

A Novel Header Matching Algorithm for Intrusion Detection Systems
Digitalized Responsive Logical Interface Application
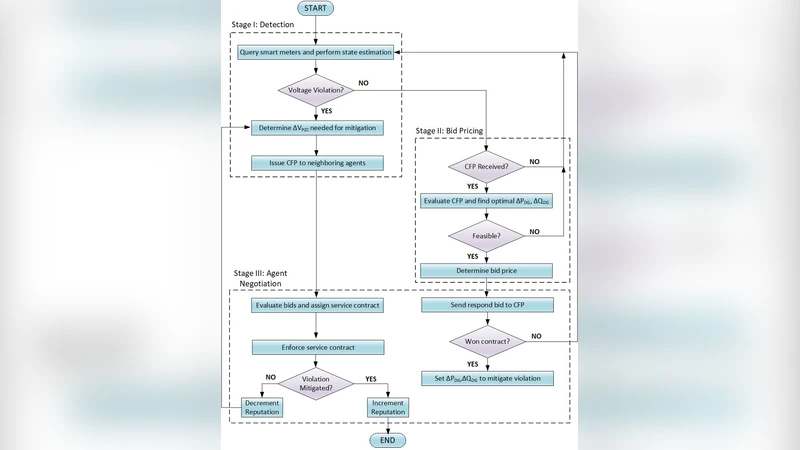
Blockchain Based Transactive Energy Systems for Voltage Regulation
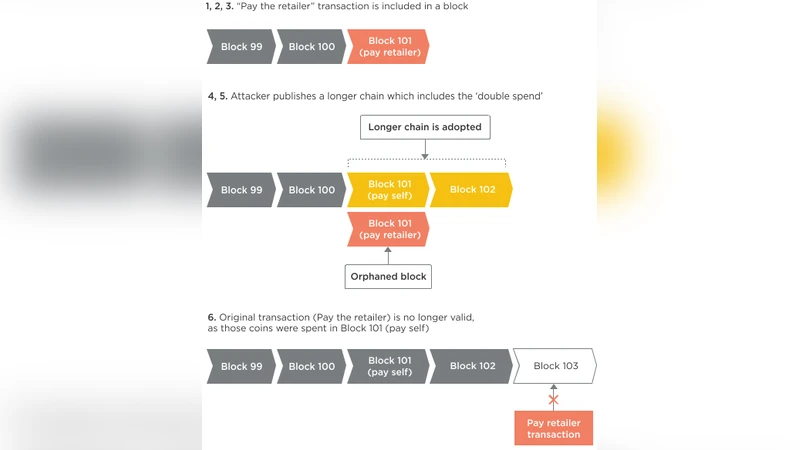
Application of Blockchain in Booking and Registration Systems of Securities Exchanges
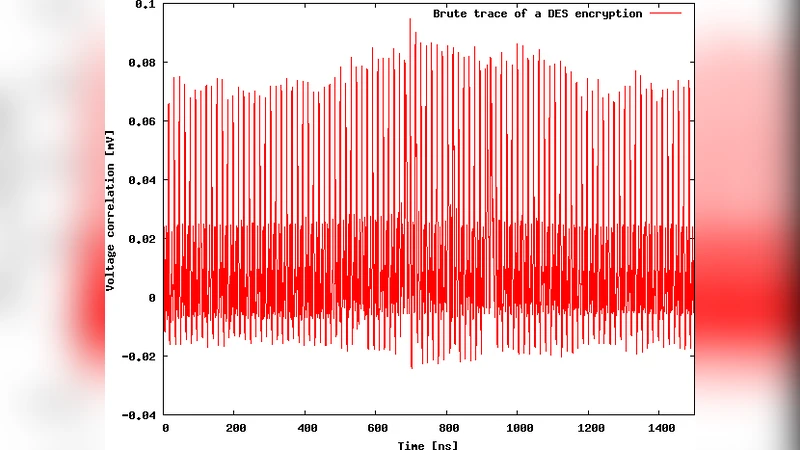
A Secure Asynchronous FPGA Architecture, Experimental Results and Some Debug Feedback
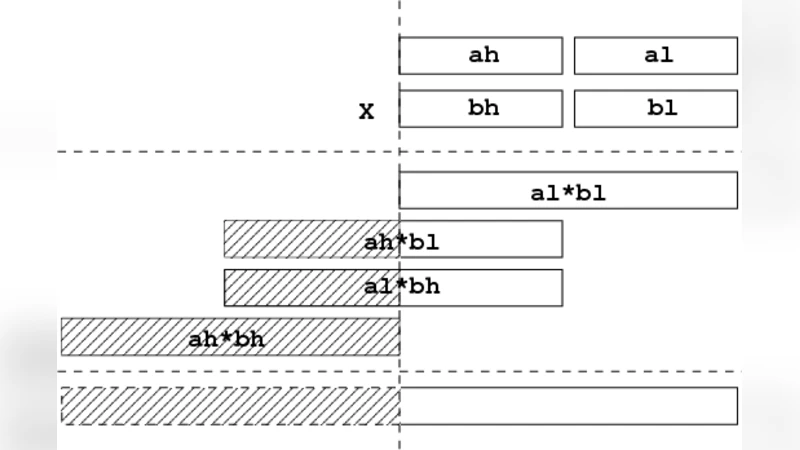
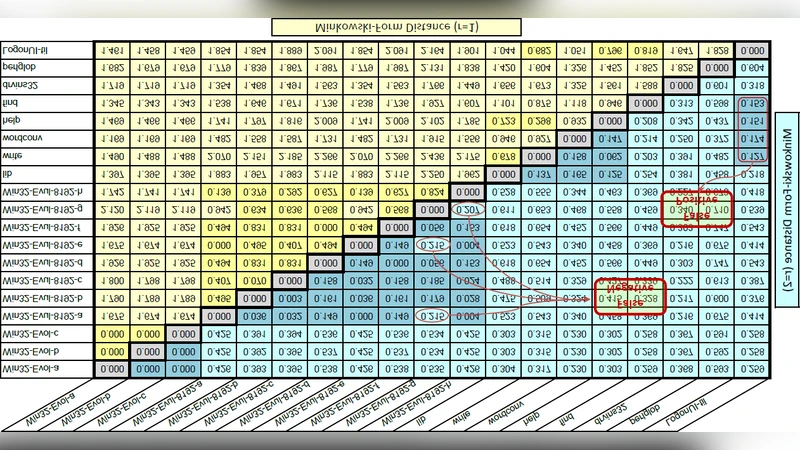
Recursive double-size fixed precision arithmetic
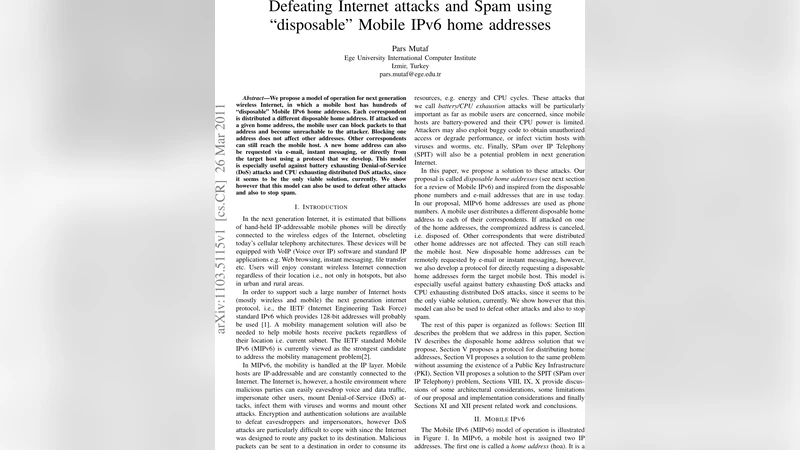
Defeating Internet attacks and Spam using "disposable" Mobile IPv6 home addresses

A quantum protocol for sampling correlated equilibria unconditionally and without a mediator
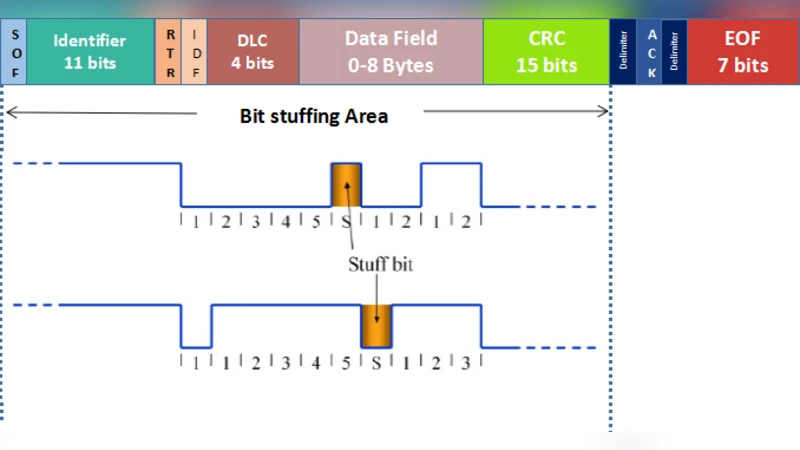
State-of-the-Art Survey on In-Vehicle Network Communication (CAN-Bus) Security and Vulnerabilities
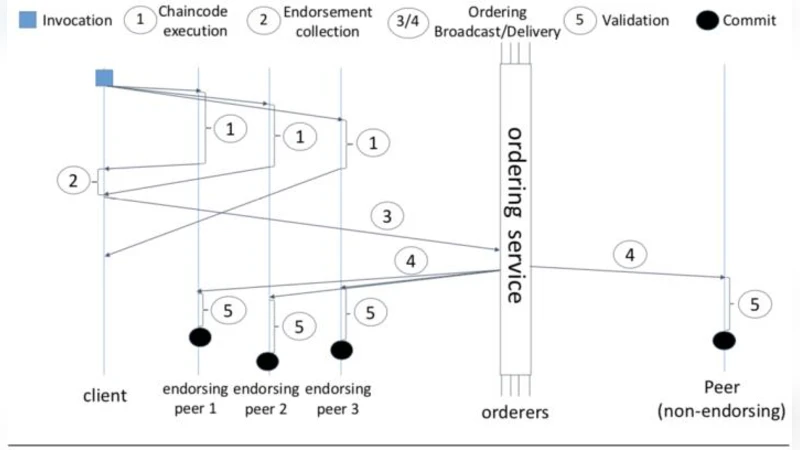
Medusa: Blockchain Powered Log Storage System

Personalized Social Recommendations - Accurate or Private?

The block cipher NSABC (public domain)

Fighting Against XSS Attacks: A Usability Evaluation of OWASP ESAPI Output Encoding
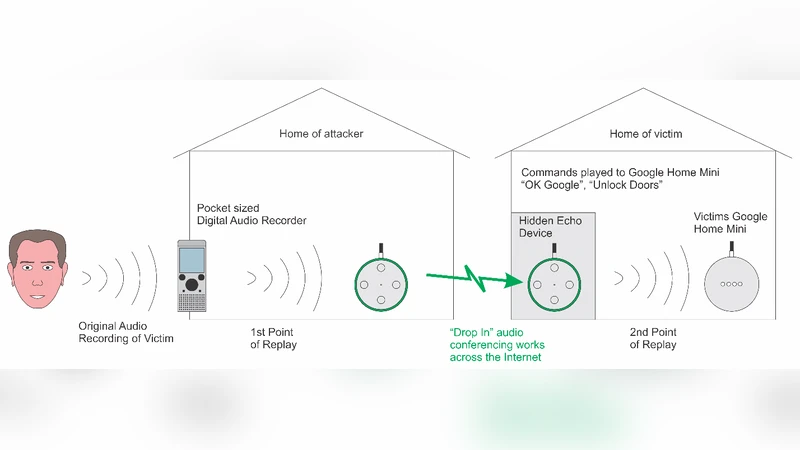
Towards Vulnerability Analysis of Voice-Driven Interfaces and Countermeasures for Replay
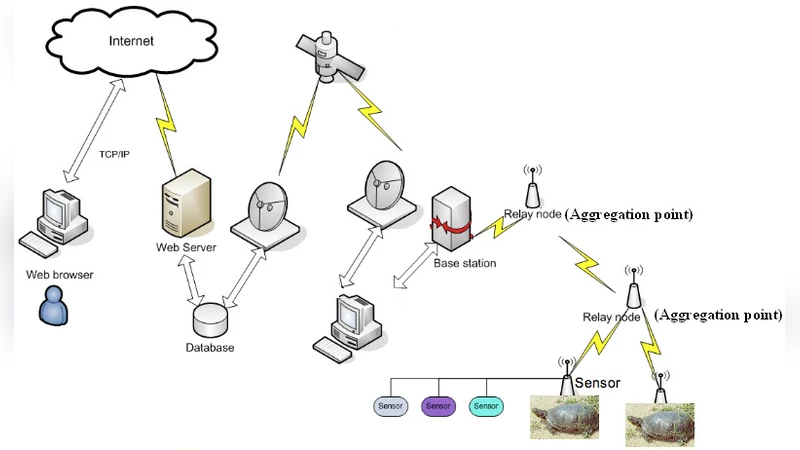
A Comparison of Link Layer Attacks on Wireless Sensor Networks
Metamorphic Virus Detection in Portable Executables Using Opcodes Statistical Feature
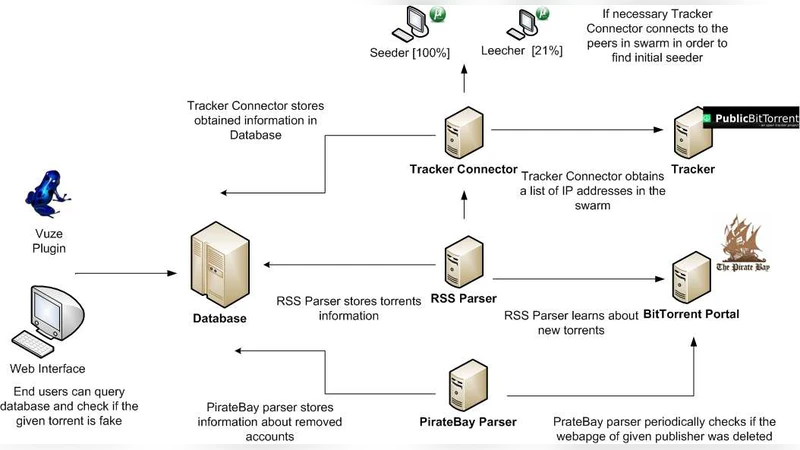
TorrentGuard: stopping scam and malware distribution in the BitTorrent ecosystem

Personal Marks and Community Certificates: Detecting Clones in Mobile Wireless Networks of Smart-Phones
Two Dimensional Random Patterns
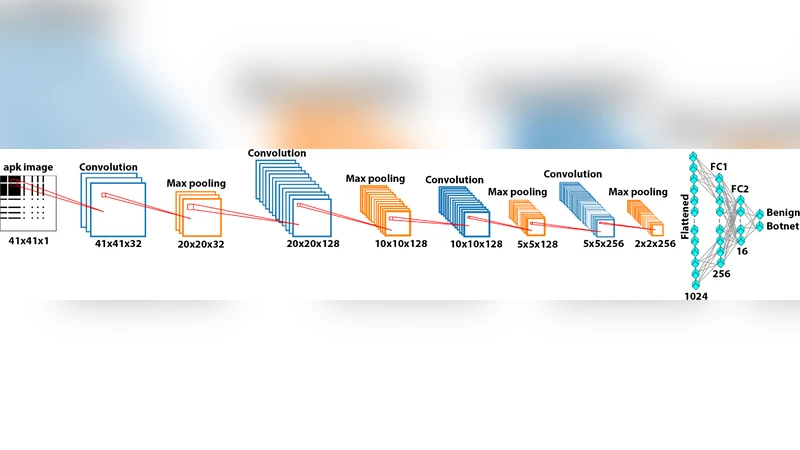
Android Botnet Detection using Convolutional Neural Networks
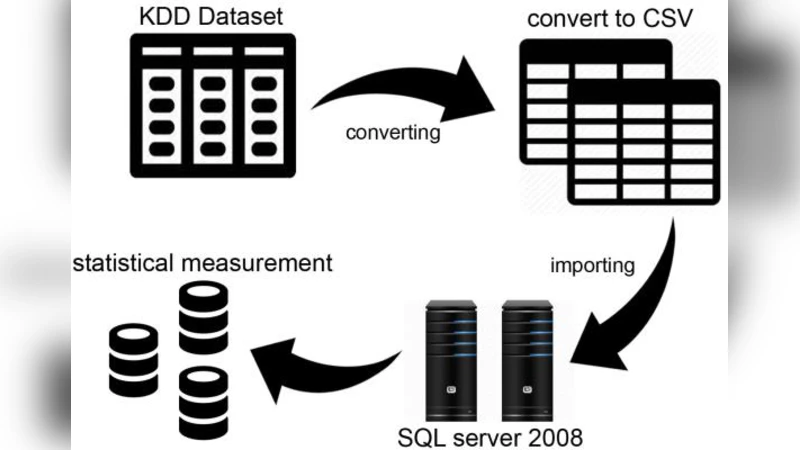
Evaluation of Machine Learning Algorithms for Intrusion Detection System

Practical Verified Computation with Streaming Interactive Proofs