Computer-Science
Wild Card Queries for Searching Resources on the Web
On Time-Bounded Incompressibility of Compressible Strings and Sequences
A Secure Multi-Party Computation Protocol for Malicious Computation Prevention for preserving privacy during Data Mining
Exact Join Detection for Convex Polyhedra and Other Numerical Abstractions
Efficient methodology for implementation of Encrypted File System in User Space
Knowledge Discovery of Hydrocyclone s Circuit Based on SONFIS and SORST
Restart Strategy Selection using Machine Learning Techniques
Buffered Aloha with K-Exponential Backoff -- Part I: Stability and Throughput Analysis
Infinite Oracle Queries in Type-2 Machines (Extended Abstract)
The Compound Capacity of Polar Codes
Population Protocols that Correspond to Symmetric Games
BPDMN: A Conservative Extension of BPMN with Enhanced Data Representation Capabilities
Randomized Incremental Construction of Compressed Quadtrees
ChOrDa: a methodology for the modeling of business processes with BPMN
A Bayesian Model for Discovering Typological Implications
A process planning system with feature based neural network search strategy for aluminum extrusion die manufacturing
System approach to synthesis, modeling and control of complex dynamical systems
A Comment on Nonextensive Statistical Mechanics
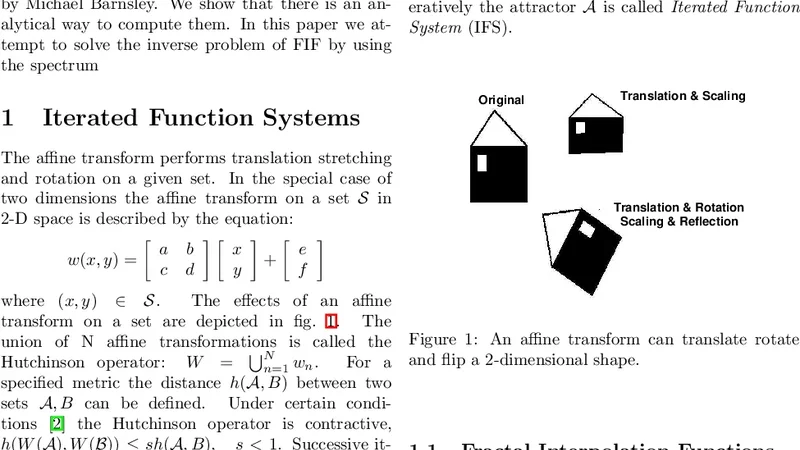
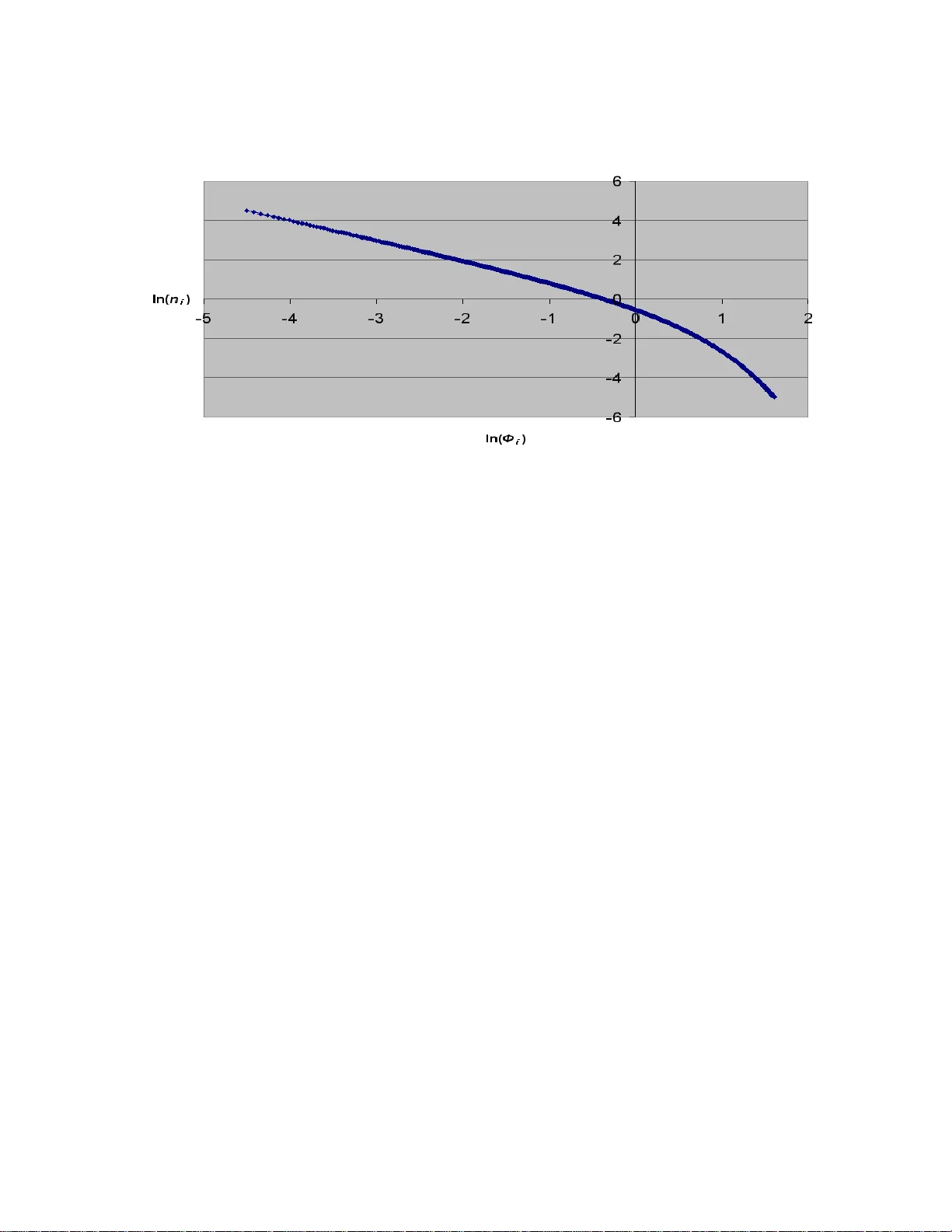
Spectrum of Fractal Interpolation Functions
How opinions are received by online communities: A case study on Amazon.com helpfulness votes
Conditional Probability Tree Estimation Analysis and Algorithms
Towards Automated Deduction in Blackmail Case Analysis with Forensic Lucid